In the ever-evolving landscape of cybersecurity, it’s crucial for businesses and individuals to stay vigilant and protect their valuable information. One solution you might want to explore is Microsoft Security Copilot, a comprehensive security service that Microsoft offers.
In the article, we will dive deeper into what is Microsoft security copilot is and its usage possibilities.
Microsoft Security Copilot is designed to proactively safeguard your organization from potential cyber threats by combining advanced AI-driven tools and the expertise of cybersecurity professionals. You can rest assured that your business’s digital assets are protected around the clock with features such as threat detection, incident response, and vulnerability management.
This service aligns with Microsoft’s broader commitment to maintaining high standards of security across its product suite. By choosing Microsoft Security Copilot, you leverage their cutting-edge technology and become part of a vast community dedicated to combating cybercrime.
Understanding Microsoft Security Copilot
Microsoft Security Copilot is a collaboration between Microsoft and OpenAI, aiming to enhance cybersecurity through robust, security-specific AI models. This section will help you understand its cybersecurity role, unique features, and OpenAI architecture.
Role in Cybersecurity
As the digital landscape evolves, it’s crucial for businesses to stay ahead in protecting their systems from emerging cyber threats. Microsoft Security Copilot is designed to support your cybersecurity measures by leveraging the power of AI.
It helps identify vulnerabilities, mitigate risks, and ensure compliance, offering you a proactive approach to protecting your digital assets. It works alongside your existing security infrastructure to strengthen your defense mechanisms against various attacks.
Unique Features
Microsoft Security Copilot offers a range of features to enhance your organization’s cybersecurity posture:
- AI-Powered Security: Security Copilot is built on advanced AI models, which enables the detection of a wide array of threats and improves real-time response capabilities.
- Tailored Solutions: Its security-specific model is designed to cater to your organization’s unique needs, allowing for customized security measures.
- Seamless Integration: You can easily integrate Security Copilot with your existing security tools and workflows, providing added value to your cybersecurity strategies.
OpenAI Architecture
Microsoft Security Copilot leverages OpenAI’s innovative architecture to deliver cutting-edge solutions for cybersecurity. OpenAI’s advanced technology makes Security Copilot capable of detecting complex threats and adapting to the ever-changing threat landscape.
The OpenAI architecture promotes continuous learning and improvement, ensuring that Security Copilot remains up-to-date and effective in protecting your organization from emerging risks. By incorporating OpenAI’s leading-edge technology, Microsoft Security Copilot is positioned to be a valuable asset in fortifying your cybersecurity efforts.
Machine Speed and Scale
The efficiency of Microsoft Security Copilot
Microsoft Security Copilot is an efficient and powerful tool to enhance security operations. The machine’s speed enables it to analyze vast amounts of data in real-time, giving you the ability to identify and respond to threats as they emerge. With this increased efficiency, your security team can focus on more proactive measures instead of being bogged down by manual analysis.
Handling Large Volumes
One of the primary advantages of Microsoft Security Copilot is its ability to handle large volumes of data easily. This scalability is essential for organizations that generate or process significant amounts of information.
The system’s machine speed and scale make it well-suited to process enormous datasets, ensuring your security operations remain nimble and adaptable to the ever-changing threat landscape.
By leveraging the power of Microsoft Security Copilot, you can enhance your organization’s security posture and minimize the risks associated with cyber threats.
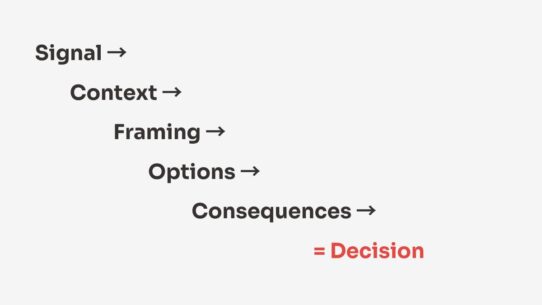
This advanced solution’s machine speed and scale combination enables rapid and effective decision-making to keep your organization’s data and operations safe.
Threat Intelligence and Reporting
Global Threat Intelligence
By tapping into Microsoft Defender Threat Intelligence, you’re harnessing the power of a comprehensive and continuously updated database of known threats. This global threat intelligence offers valuable insights on emerging risks, allowing you to stay ahead of potential incidents.
The integration of this data into Microsoft Security Copilot enables you to detect trends, anticipate possible attacks, and put suitable measures in place to secure your systems.
Incident Reporting
Staying informed of incidents occurring within your organization or those that pose a potential threat is essential. Microsoft Security Copilot streamlines the incident reporting process, ensuring you receive timely and accurate information.
This allows you to act quickly to prevent or mitigate the effects of an attack. By utilizing detailed incident reports in Microsoft Security Copilot, you can also review and analyze events, helping you identify patterns and predict future risks effectively.
With the support of global threat intelligence, Microsoft Security Copilot’s incident reporting capabilities enable you to be proactive and strategic in your approach to cybersecurity. This ensures you maintain a robust security posture and protect your valuable data and infrastructure.
Defense Tools in Microsoft Security Copilot
Microsoft Sentinel
Microsoft Sentinel is an advanced cloud-native Security Information and Event Management (SIEM) tool that helps you identify and respond to threats seamlessly. With Microsoft Sentinel, you get a powerful platform to analyze your data, helping you gain insights and detect anomalies within your network.
It integrates easily with various data sources, including Microsoft 365 and third-party solutions, ensuring comprehensive threat visibility across your entire environment.
Microsoft Sentinel intelligently sifts through your data, utilizing machine learning and artificial intelligence capabilities, detecting and prioritizing security incidents.
You can automate your responses with built-in playbooks or create custom playbooks tailored to your organization’s unique requirements.
Microsoft 365 Defender
Microsoft 365 Defender is designed to secure your Microsoft 365 environment from threats by leveraging advanced detection and response capabilities. This comprehensive defense tool covers multiple attack surfaces within your Microsoft 365 environment, such as emails, identities, files, and endpoints.
By integrating with other Microsoft security services like Microsoft Defender for Office 365 and Microsoft Defender for Endpoint, Microsoft 365 Defender offers a unified approach to security management.
You can easily track incidents and automate remediation tasks through the Microsoft 365 security center, ensuring your organization’s data is always protected.
Microsoft Intune
Microsoft Intune is a cloud-based Unified Endpoint Management (UEM) solution that helps you manage and secure all your organization’s devices, including mobile phones, tablets, and laptops. With Intune, you can define and enforce policies to protect your organization’s data, ensuring compliance with industry regulations.
Intune’s key features include deploying applications, configuring security settings, and safeguarding your company data from unauthorized access. Intune also integrates with other Microsoft Security Copilot tools, providing a holistic approach to endpoint security in your organization.
By employing Microsoft Security Copilot’s defense tools – Microsoft Sentinel, Microsoft 365 Defender, and Microsoft Intune – you can ensure your network, endpoints, and data remain secure against evolving threats. Remember to explore each tool’s capabilities to determine your organization’s most effective security solutions.
Role of Natural Language Processing
Language Model
Natural language processing (NLP) is an essential component of Microsoft Security Copilot, allowing the system to understand and interpret spoken or written language. You’ll find that language models play a vital role in converting the input into a structured format that Microsoft Security Copilot can use.
Specifically, advanced language models, such as GPT-3 or BERT, help process a wide range of user inputs, allowing the system to respond to complex queries.
For example, if you ask for assistance fixing a security vulnerability, the language model will break down your query and identify the key information. By doing so, the system can provide a clear response tailored to your needs.
Responsible AI
The concept of responsible AI is integrated into Microsoft Security Copilot to ensure ethical AI usage and trustworthiness when handling sensitive data. As a user, you can expect the system to follow guidelines prioritizing transparency, fairness, and privacy.
Microsoft Security Copilot adheres to these principles:
- Transparency: The AI’s decision-making process is made clear, and you’ll receive evidence-backed recommendations in an understandable manner.
- Fairness: Efforts are made to reduce biases and avoid favoring any particular group, ensuring all users get unbiased results and recommendations.
- Privacy: Your data is handled with utmost care, following industry-standard privacy practices and ensuring that any information generated stays confidential and secure.
By incorporating these principles, Microsoft Security Copilot becomes a reliable tool you can trust to handle security-related tasks responsibly.
Incident Response and Remediation
In your organization, swift incident response and effective remediation are crucial in maintaining security. Microsoft Security CoPilot offers the tools and techniques to identify, address, and mitigate potential threats quickly.
You must be ready to respond confidently and knowledgeably when a security incident occurs. Microsoft Security CoPilot provides a clear and focused approach to the incident response process, ensuring you address threats efficiently.
Using advanced analytics, threat intelligence, and seamless integration with other Microsoft security services, CoPilot empowers you to take swift action against any potential hazard.
Remediation is another critical aspect of your security strategy. Microsoft Security CoPilot helps identify vulnerabilities and provides guidance on the best action to fix the issues.
With the expertise of Microsoft’s security engineers at your disposal, you can expect a comprehensive understanding of the risks, the most appropriate mitigation measures, and the necessary steps to prevent future occurrences.
By implementing Microsoft Security CoPilot in your organization, you equip yourself with the capability to handle security incidents decently and informally.
Swift incident response and effective remediation efforts will bolster your overall security posture, making your organization a less attractive target for attackers.
Posture Management and Risk Exposure
Regarding securing your organization’s digital assets, Microsoft Security Copilot offers posture management and risk exposure monitoring to provide you with a comprehensive security solution. This section covers the essential aspects of these features in a clear, confident manner.
Posture management is an essential part of securing your IT infrastructure. By continuously analyzing and monitoring your organization’s security posture, Microsoft Security Copilot helps you identify and address potential vulnerabilities before they cause any harm.
This process involves assessing your systems, networks, and applications for weaknesses, outdated software, and improperly configured settings.
The key to successful posture management is to stay proactive in maintaining the security of your systems. Microsoft Security Copilot makes this easier for you by providing alerts and actionable insights when issues arise. This enables you to address vulnerabilities and prevent cyberattacks swiftly.
On the other hand, risk exposure refers to the likelihood of your organization suffering a security breach due to vulnerabilities in your IT environment. By keeping track of your risk exposure, you can identify areas of concern and prioritize security measures.
Microsoft Security Copilot provides various tools to help you monitor and manage your risk exposure. These include:
- Automated risk assessments: Regularly evaluate the security risks in your IT environment, identifying potential vulnerabilities and weak points.
- Risk scoring: Prioritize your threats by assigning risk scores based on the severity of each vulnerability and its potential impact on your organization.
- Visualization tools: Get a clear overview of your organization’s risk exposure through dynamic charts, graphs, and tables that provide actionable insights.
By utilizing Microsoft Security Copilot’s posture management and risk exposure monitoring features, you can ensure your organization is better protected and prepared for potential cyberattacks. Stay vigilant in maintaining your IT security to keep your organization safe and secure.
Catch What Others Miss: The Asymmetric Battle
In the ever-evolving world of cybersecurity, you are constantly faced with an asymmetric battle against attackers. The Microsoft Security Copilot aims to provide you with the necessary tools and resources to stay one step ahead of these adversaries.
As you protect your digital assets, it’s essential to be aware that attackers often capitalize on the smallest gaps in security measures. By integrating the Microsoft Security Copilot into your cybersecurity strategy, you can catch what others miss and reduce the likelihood of falling victim to these threats.
The asymmetric nature of this battle means that while attackers need to succeed only once, you have to be consistently vigilant to prevent breaches. The Microsoft Security Copilot utilizes advanced analytics and threat intelligence to help you identify and address vulnerabilities that might otherwise go unnoticed.
In addition to helping you spot the gaps in your defenses, the Microsoft Security Copilot also seeks to simplify your security workflow. This is achieved by consolidating your security tools and providing actionable insights that allow you to make informed decisions about your organization’s cybersecurity posture.
By leveraging the power of Microsoft Security Copilot, you can gain a significant advantage in the asymmetric battle against cyber threats. Stay confident, knowledgeable, and proactive as you secure your digital environment and catch what others might miss.
Increasing Value for Cybersecurity Professionals
As a cybersecurity professional, you are constantly looking for ways to streamline your work, improve security measures, and stay updated in the ever-evolving threat landscape. Microsoft Security Copilot brings immense value to your work by providing a centralized location for managing security tools, policies, and configurations.
With Microsoft Security Copilot, you can quickly and easily access valuable security insights and recommendations tailored to your organization. It lets you stay on top of current threats and provides immediate context with real-time threat intelligence.
This greatly benefits your decision-making process and helps you stay proactive in mitigating cyber risks.
By integrating with other Microsoft services, Security Copilot centralizes the management of these tools, making it simple to track security policies, monitor performance, and apply necessary updates to your systems. This integration saves time and resources, allowing you and your team to focus on essential security tasks.
From a skills development standpoint, Microsoft Security Copilot also enables you to upskill your expertise by providing access to valuable learning resources, webinars, and community-driven knowledge sharing. This continuous learning empowers you to hone your skills and stay ahead in your cybersecurity career.
Microsoft Security Copilot enhances your cybersecurity management capabilities and helps you grow and develop as a professional in this field, making it a valuable asset in your daily work and career progression.
Summary: What is Microsoft Security Copilot
Microsoft Security Copilot provides you with a comprehensive security solution for your organization. It integrates seamlessly with your existing systems and offers enhanced protection against cyber threats. Leveraging AI and automation it simplifies security management and helps you stay ahead of potential risks.
Adopting Microsoft Security Copilot allows you to expect improved monitoring, threat detection, and incident response times. With a wide array of features, such as multi-factor authentication, threat intelligence, and device management, you can better safeguard your organization’s data and assets.
Microsoft Security Copilot is a valuable investment in your organization’s security infrastructure. It equips you with the tools and resources needed to protect your systems and data, allowing you to focus on what matters most – growing your business.
Ready to take the next step? Visit larsbirkeland.com to learn AI in cybersecurity!
FAQ
What is Microsoft Security Copilot?
Microsoft Security Copilot is an AI-powered security analysis tool that enables security professionals to respond to threats quickly, process signals at machine speed, and assess risk exposure in minutes.
How is Microsoft Security Copilot different from other AI security products?
Microsoft Security Copilot is the only security AI product that combines a specialized large language model (LLM) with security-specific capabilities from Microsoft. Security Copilot’s capabilities incorporate a growing set of security-specific skills informed by Microsoft’s unique global threat intelligence and more than 65 trillion daily signals.
What are the benefits of using Microsoft Security Copilot?
The benefits of using Microsoft Security Copilot include accelerated incident response, enhanced threat detection, and augmented human capabilities. By leveraging AI, organizations can gain more accurate results and proactively identify future threats and vulnerabilities.
How does Microsoft Security Copilot work?
Microsoft Security Copilot uses generative AI to help detect threats, manage incidents, and improve security posture. It integrates insights and data from security tools and delivers guidance tailored to your organization. Security Copilot also allows users to ask questions in natural language and receive actionable responses.
Does Microsoft Security Copilot work with other Microsoft Security products?
What are some potential risks associated with Microsoft Security Copilot?
How can organizations incorporate Microsoft Security Copilot into their security strategy?
Organizations can incorporate Microsoft Security Copilot into their security strategy by identifying regulatory, financial, and reputational risks and by identifying what data should be collected and how they should be processed based on the current risk framework and organizational values. The AI data set processing model can be defined based on previous risk assessments.