Incorporating AI in cybersecurity risk assessment has become a necessity for businesses and organizations. As cyber threats continue to grow in complexity, AI-driven solutions are being developed to proactively identify vulnerabilities, detect anomalies, and respond to security incidents. With artificial intelligence playing a vital role in protecting critical infrastructure and sensitive data, understanding its benefits and implementations is crucial for professionals in the field.
AI-enabled cybersecurity tools can parse vast amounts of data, identify patterns, and analyze network activity at scale. With continually adapting and evolving machine learning algorithms, these systems can quickly detect and offset potential risks before they cause damage. By implementing AI in risk management strategies, businesses can effectively stay ahead of emerging threats while ensuring compliance with ever-changing data protection regulations.
Key Takeaways
- The integration of AI in cybersecurity makes risk assessment more proactive and efficient.
- AI-driven tools identify and detect threats rapidly, allowing for faster response and mitigating potential damage.
- By incorporating AI systems, businesses can ensure regulatory compliance and improve their overall cybersecurity posture.
Understanding AI and Cybersecurity
AI-powered cybersecurity technologies can play a crucial role in mitigating cyber threats and improving risk assessment. This section will discuss how artificial intelligence is utilized in cybersecurity and its role in assessing cyber risks.
AI in Cybersecurity
With machine learning and deep learning advancements, AI has significantly improved detection and response to cyber threats. AI-based tools can analyze large volumes of data, quickly identifying patterns that suggest malicious activity. By leveraging AI capabilities, you can proactively monitor your network, identify vulnerabilities, and predict security incidents before they occur.
Machine learning algorithms are particularly useful in detecting unknown threats or zero-day exploits. These algorithms can be trained to learn from millions of malicious and benign software samples, allowing them to recognize and prevent attacks even when specific signatures or patterns are unknown.
AI-powered security tools can also improve incident response by automating tasks such as malware analysis, threat hunting, and decision-making. This helps your security team respond more quickly and efficiently, reducing potential cyberattack damage.
Risk Assessment in Cybersecurity
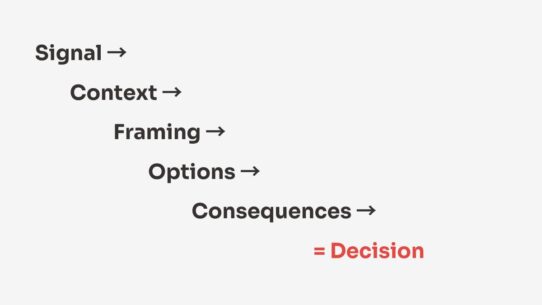
AI-driven risk assessment in cybersecurity involves the use of machine learning models that predict the probability of a cyberattack and its potential impact. These models can analyze factors such as network configurations, historical data, user behaviors, and external threat intelligence.
By leveraging AI in risk assessment, your organization can gain better insights into the potential vulnerabilities of your systems and the risks associated with specific assets. These insights can help prioritize investment in security measures and make informed decisions on risk mitigation strategies.
Additionally, AI models can support continuous monitoring and real-time risk analysis, allowing for quick response to changes in the threat landscape. This enables adaptive cybersecurity strategies that can evolve as new threats emerge and your organization’s environment changes.
AI is critical in cybersecurity and risk assessment. By harnessing the power of AI, you can improve your organization’s ability to detect and respond to cyber threats and make better-informed decisions about your cybersecurity strategy.
AI Systems and Cybersecurity Challenges
AI Systems Vulnerabilities
As you integrate AI systems into your organization’s cybersecurity infrastructure, it’s important to be aware of the security risks these systems can introduce. AI systems can be vulnerable to several attack vectors, including:
- Adversarial attacks: Cybercriminals can exploit AI models by manipulating the input data to generate inaccurate or malicious outputs.
- Data poisoning: Malicious actors can intentionally introduce corrupted or false information into your AI training data, which can lead to poor decision-making.
- Model stealing: Unauthorized access to your AI models may compromise sensitive information or result in malicious actors using the models for their own purposes.
In order to mitigate these vulnerabilities, you should:
- Regularly update and monitor your AI models for unexpected behavior
- Ensure proper data verification and validation procedures are in place
- Implement access control measures, such as encrypting your AI models and data
Cybersecurity Challenges in AI
Addressing vulnerabilities in AI systems doesn’t come without its own set of challenges. When integrating AI into your cybersecurity risk assessment, keep in mind:
- Increased attack surface: The more systems and interfaces you have, the more potential entry points for cybercriminals to exploit. AI can introduce new vectors that you must be prepared to protect.
- Complexity: The algorithms used in AI systems are often highly complex, making it difficult to detect risks and vulnerabilities in real time.
- Ethical concerns: There’s a growing debate around the use of AI in cybersecurity, particularly concerning its potential to contribute to unethical surveillance or discrimination practices.
To address these challenges, you should:
- Implement a comprehensive security policy for your AI systems, which includes regular audits and vulnerability assessments
- Establish clear guidelines and protocols for the ethical use of AI within your organization
- Collaborate with other organizations and industry professionals to share knowledge and resources for improving AI security practices.
AI in Risk Management
Understanding AI Risk Management Framework
When dealing with AI in cybersecurity, it’s important to understand the AI risk management framework. This framework helps you plan and execute robust cybersecurity measures while minimizing the associated risks. A comprehensive AI risk management framework encompasses aspects such as risk assessment, governance, security policies, and enterprise security. By implementing an effective framework, you can be better prepared to handle various cybersecurity threats.
To begin, you should conduct AI risk and impact assessments, which involve analyzing potential risks tied to AI applications in your organization. These assessments should consider the environment, technologies, and processes behind your AI deployment. Keep a keen eye on vulnerabilities, possible threats, and their consequences.
AI for Risk Assessment and Governance
Implementing AI in your risk assessment and governance processes can significantly enhance your cybersecurity efforts. AI-powered tools can help you identify potential threats and vulnerabilities more effectively, leading to better decision-making and mitigation strategies. Furthermore, AI can enable you to take a proactive approach to cybersecurity by forecasting potential attack vectors based on historical data.
Establish clear and consistent security policies throughout your organization, ensuring proper enforcement and adherence to these regulations. By incorporating AI in enterprise security, you can optimize policy enforcement, real-time monitoring, and incident response.
To effectively utilize AI in risk management, consider implementing risk mitigation measures that align with your risk and impact assessments. These measures could include vulnerability management, security audits, and access control mechanisms. Integrate AI solutions to periodically reassess your organization’s risk landscape and determine whether your established protocols remain effective.
With this knowledge, you can harness AI capabilities to efficiently manage and control your organization’s risk posture in the realm of cybersecurity.
Role of Data in Cybersecurity Risk Assessment
Importance of Data
In today’s digital world, data plays a critical role in every aspect of life. In the context of cybersecurity risk assessment, data is the foundation upon which you build your understanding of potential threats and vulnerabilities. With data’s increasing volume, variety, and complexity, effective data ingestion and analytics are essential for successful risk assessments.
The analytics process can help you identify patterns, trends, and anomalies in your data, allowing you to pinpoint potential vulnerabilities and threats. High-quality data contributes to accurate and timely insights, ultimately assisting you in the decision-making process concerning risk management and mitigation strategies.
Protecting Sensitive Data with AI
Handling sensitive data, such as personal information or trade secrets, requires extra care and attention. Artificial intelligence (AI) can be a powerful tool in identifying and protecting sensitive data within your organization’s network. By leveraging AI algorithms, you can quickly scan vast amounts of data to detect and classify sensitive information.
AI-based solutions can also help you monitor and manage access to sensitive data. AI can detect insider threats, unauthorized access, and data breaches by analyzing user behavior and access patterns. This proactive approach to data protection with AI ensures that your sensitive data remains secure in an ever-evolving threat landscape.
The role of data in cybersecurity risk assessment is indispensable. High-quality data ingestion and analytics are crucial for identifying threats and vulnerabilities, and AI technologies can be employed to protect sensitive data better. By staying informed and proactive in your cybersecurity measures, you’re well-equipped to defend your organization against the constantly evolving cyber threat landscape.
Regulatory Compliance and AI
As a professional working in cybersecurity, it’s critical to understand how regulatory compliance requirements and the evolving AI technology landscape are linked. AI-driven solutions are becoming key players in cybersecurity risk assessments and ensuring adherence to regulations like the NIST cybersecurity framework.
In the pursuit of maintaining regulatory compliance, you need to be cognizant of the capabilities and limitations of AI. AI-based cybersecurity tools can help you detect and prevent breaches, predict possible attack vectors, and provide in-depth analysis of your organization’s security posture.
These solutions can be essential in meeting regulatory standards and demonstrating your organization’s commitment to securing sensitive information and systems.
Aligning AI technologies with regulatory frameworks like NIST goes hand-in-hand with tapping their potential in cybersecurity risk assessment. As you deploy AI-powered tools, you’ll need to ensure that they’re abiding by the guidelines imposed by policymakers. In doing so, not only will your organization achieve compliance, but you’ll also improve the efficiency and efficacy of your cybersecurity measures.
Collaborating with policymakers is also crucial to ensure that AI applications in cybersecurity are properly regulated and standardized. Since AI technology is still a rapidly evolving field, establishing a harmonious relationship between policymakers, cybersecurity professionals, and AI solution developers can set the stage for a secure future in which AI is essential to regulatory compliance efforts.
Integrating AI in regulatory compliance and cybersecurity risk assessments empowers your organization to stay ahead of emerging threats and demonstrate a strong commitment to security.
Remember the importance of adhering to existing guidelines, such as NIST, and fostering collaboration with policymakers to harness the full potential of AI in this crucial domain.
AI and Security Professionals
AI’s Impact on Cybersecurity Teams
As a security professional, it’s essential to acknowledge the transformative power AI brings to cybersecurity risk assessment. AI-driven tools and techniques can improve the efficiency and effectiveness of your cybersecurity teams. By automating repetitive tasks, AI allows your team members to focus on more complex and critical issues.
In addition to enhancing threat detection capabilities, AI can help you identify previously unknown vulnerabilities and develop proactive strategies. AI-powered systems can also streamline incident response and decision-making processes by analyzing large volumes of data and providing actionable insights. As a result, your cybersecurity teams can respond to threats more quickly and precisely.
Role of Chief Information Security Officer
The rise of AI in cybersecurity has significant implications for the Chief Information Security Officer (CISO) role. As a CISO, staying updated with AI advancements and understanding how these technologies apply to your organization is crucial.
With AI playing an increasingly prominent role, your responsibilities may include ensuring the proper integration of AI into your cybersecurity infrastructure. This may involve collaborating closely with AI specialists and fostering a culture of continuous learning and skills development within your security teams.
Managing the ethical implications of AI is also of paramount importance. As CISO, you should establish clear guidelines and protocols for your organization’s use of AI in cybersecurity, ensuring that ethical considerations are always at the forefront.
By staying informed on AI technology and adapting to its implications, you can leverage its capabilities as a security professional or CISO to bolster your organization’s cybersecurity risk assessment and response strategies.
Machine Learning in Cybersecurity Risk Assessment
Machine Learning Models and Cybersecurity
Implementing machine learning models in your cybersecurity risk assessment process can enhance your organization’s ability to assess and respond to threats. By autonomously analyzing enormous quantities of data, these models can learn patterns and detect anomalies that might indicate potential risks.
Selecting suitable machine learning models is a critical first step. There are several types of models that you can utilize, including supervised learning, unsupervised learning, and reinforcement learning models. The choice of the model will depend on your specific cybersecurity requirements. By incorporating machine learning into your security infrastructure, you’ll significantly improve your abilities to:
- Accurately identify potential threats.
- Minimize false positives and negatives.
- Automate incident response.
Threat Detection with Machine Learning
Machine learning’s capabilities can be effectively applied to threat detection, helping you stay ahead of various cybersecurity threats. For instance, machine learning algorithms can monitor and analyze:
- Network traffic patterns
- System logs
- User behavior
This monitoring facilitates early detection of suspicious activities or behavior and allows for timely intervention to prevent data breaches and malicious attacks.
Anomaly detection is a common use case for machine learning in threat detection. By building a baseline of normal behavior, machine learning models can identify deviations and flag them for further analysis. Moreover, applying predictive analytics helps you anticipate potential risks by examining historical data and identifying patterns associated with incidents.
Some examples of machine learning techniques used in threat detection include:
- Clustering algorithms for discovering unusual patterns in data
- Neural networks for identifying complex relationships between variables
- Decision trees and random forests for classification and risk estimation
By incorporating machine learning into your cybersecurity risk assessment process, you’ll benefit from continuous learning and improvement as these models adapt to emerging threats and evolving risk landscapes.
Automating Risk Assessment with AI
In the field of cybersecurity, risk assessment plays a crucial role in protecting your organization’s valuable assets. With the rapid growth of technology and the increasing sophistication of cyber threats, automating risk assessment with AI can make a significant difference in your cybersecurity posture.
By leveraging AI, you can automate the process of identifying potential threats and vulnerabilities in your system. This allows for greater scalability in assessing risks, as AI systems can quickly analyze vast amounts of data, making it more efficient than relying solely on manual efforts. As a result, you can focus more on addressing the high-priority risks and ensuring your organization’s security.
Real-time monitoring is another advantage of using AI in cybersecurity risk assessment. Instead of waiting for scheduled security audits, AI-powered tools can continuously monitor your systems for any indications of risks or threats. This enables you to respond faster to incidents and minimize potential damages. Additionally, AI systems can learn and adapt to new threats, constantly improving their detection capabilities and keeping you one step ahead of attackers.
Incorporating AI in your cybersecurity risk assessment process can lead to more accurate and efficient assessments. For instance, AI can help:
- Automate data collection and analysis: AI-powered tools can gather and analyze data from various sources, such as logs and network traffic, enabling you to identify patterns and correlations that might signify potential risks.
- Enhance vulnerability scanning: AI can aid in detecting vulnerabilities in your system more effectively, identifying potential risks that traditional methods might have missed.
- Improve threat intelligence: AI algorithms can analyze threat data from various sources and provide insights into cybercriminals’ latest trends and tactics, helping you stay informed and prepared.
Remember, while AI can significantly improve your cybersecurity risk assessment process, it should not be seen as a complete replacement for human expertise. A combination of AI and human insight is essential for developing a robust, comprehensive, and responsive risk management strategy.
Implication of AI on Businesses and Engineers
With the rapid advancement of Artificial Intelligence (AI) in various industries, its impact on cybersecurity risk assessment is becoming increasingly significant. As a business owner or engineer, it’s essential to understand how AI can help protect your organization from potential security threats and financial risks.
AI in Cybersecurity Strategy for Businesses
Adopting AI in your cybersecurity strategy offers several benefits that can improve your organization’s security posture. AI-driven tools can:
- Automate threat detection: By employing AI algorithms, your cybersecurity system can automatically identify and respond to suspicious activities or potential threats in real-time.
- Prioritize risks: AI-powered risk assessment can help you prioritize risks according to their potential impact on your business, allowing you to allocate resources effectively.
- Improve incident response: AI can assist in the rapid analysis of security incidents and contribute to streamlining the response process, significantly reducing the potential damage caused by an attack.
To leverage these benefits, it’s crucial to integrate AI into your existing cybersecurity framework. This may involve adopting AI-driven security tools, updating policies to accommodate AI capabilities, and providing training to your security team on the use of AI technologies.
Conclusion: AI In Cybersecurity Risk Assessment
In the ever-evolving landscape of cybersecurity, AI plays a crucial role in risk assessment. As you incorporate AI-driven tools and techniques into your cybersecurity strategies, you’ll notice substantial improvements in identifying and mitigating potential threats.
AI helps you analyze content and traffic patterns to detect anomalies more efficiently. By constantly monitoring and learning from your network data, AI algorithms can identify even the subtlest shifts and swiftly flag any suspicious behavior. This heightened visibility enhances the trust you have in your security systems.
As you rely on AI for cybersecurity risk assessment, it’s important to remember that your tools and methods need regular updates and maintenance. As technology advances, so do the attackers and their tactics. Staying ahead will require consistent investment in AI solutions and the security experts who manage them.
While AI unlocks new potentials in assessing risks, it’s crucial not to overstate its capabilities. Artificial intelligence is not a magical solution to all your security problems; it functions best as part of a comprehensive cybersecurity strategy, working with traditional human expertise.
By embracing the power of AI in cybersecurity risk assessment, you’ll be better equipped to protect your assets and maintain the trust and integrity of your systems. Remember to stay informed and vigilant, and always strive to improve your security posture in the face of ever-changing threats.
Ready to take the next step? Visit larsbirkeland.com to learn AI in cybersecurity!
FAQ
What is the role of AI in risk assessments?
AI technologies are particularly useful in risk assessment due to their ability to quickly detect, analyze, and respond to threats. AI-powered risk assessments can produce more accurate results and proactively identify potential future threats and vulnerabilities. This enables organizations to put measures in place to prevent potential security threats from occurring and more effectively remediate existing risk gaps.
What are the benefits of using AI in cybersecurity risk assessments?
The benefits of using AI in cybersecurity risk assessments include accelerated incident response, enhanced threat detection, and augmented human capabilities. By leveraging AI, organizations can gain much more accurate results and proactively identify potential future threats and vulnerabilities.
What are some of the major risks associated with AI in cybersecurity?
Some of the major risks associated with AI in cybersecurity include cyber attacks optimization, data privacy and security concerns, and the potential for AI to be used for malicious purposes. It is important to actively address these risks through responsible AI development, robust regulations, ongoing research, and collaboration between various stakeholders to ensure that AI technologies are developed and deployed in a responsible and ethical manner.
What are some of the top uses of AI in cybersecurity?
Some of the top uses of AI in cybersecurity include identifying unknown threats, handling large amounts of data, learning more over time, enhancing threat detection, and providing predictive insights into potential risks.
What are some scenarios when it might be wise to avoid using AI in cybersecurity?
It might be wise to avoid using AI in cybersecurity if you have a small or outdated dataset, lack the necessary skills or resources, rely heavily on legacy infrastructure, or lack the necessary hardware or cloud resources.
How can organizations incorporate AI into their risk assessment strategy?
The first step in incorporating AI into a risk assessment strategy is to identify regulatory, financial, and reputational risk. It is also crucial to identify what data should be collected and how they should be processed based on the current risk framework and organizational values. The AI model of processing data sets can be defined based on previous risk assessments. The type of data to use and the sources are critical considerations.