Cyber threats are soaring, with global cybercrime damages projected to surpass $10 trillion by 2026. As attacks grow in scale and complexity, organizations face mounting pressure to defend their data, systems, and reputation.
This guide to iso 27032 unpacks the leading international standard for building resilient cybersecurity frameworks in today’s digital-first world. Whether you are an IT leader, CISO, or business owner, understanding iso 27032 is essential to protect your organization from evolving risks.
Ready to future-proof your business? In this article, we share expert insights, actionable steps, and real-world examples to help you implement iso 27032, strengthen digital trust, and stay ahead of cybercriminals.
Understanding ISO 27032: Scope, Purpose, and Relevance in 2026
Cyber threats are evolving at a pace that leaves many organizations struggling to keep up. In this environment, iso 27032 has become a beacon for businesses aiming to secure their digital future. Originally published in 2012, iso 27032 has seen significant updates, most recently reflected in its 2023 and upcoming 2025 editions. These changes ensure the standard remains relevant in a world dominated by cloud computing, remote work, and ever-expanding attack surfaces. For a deeper dive into the latest updates and scope, you can visit the ISO/IEC 27032:2023 Overview.
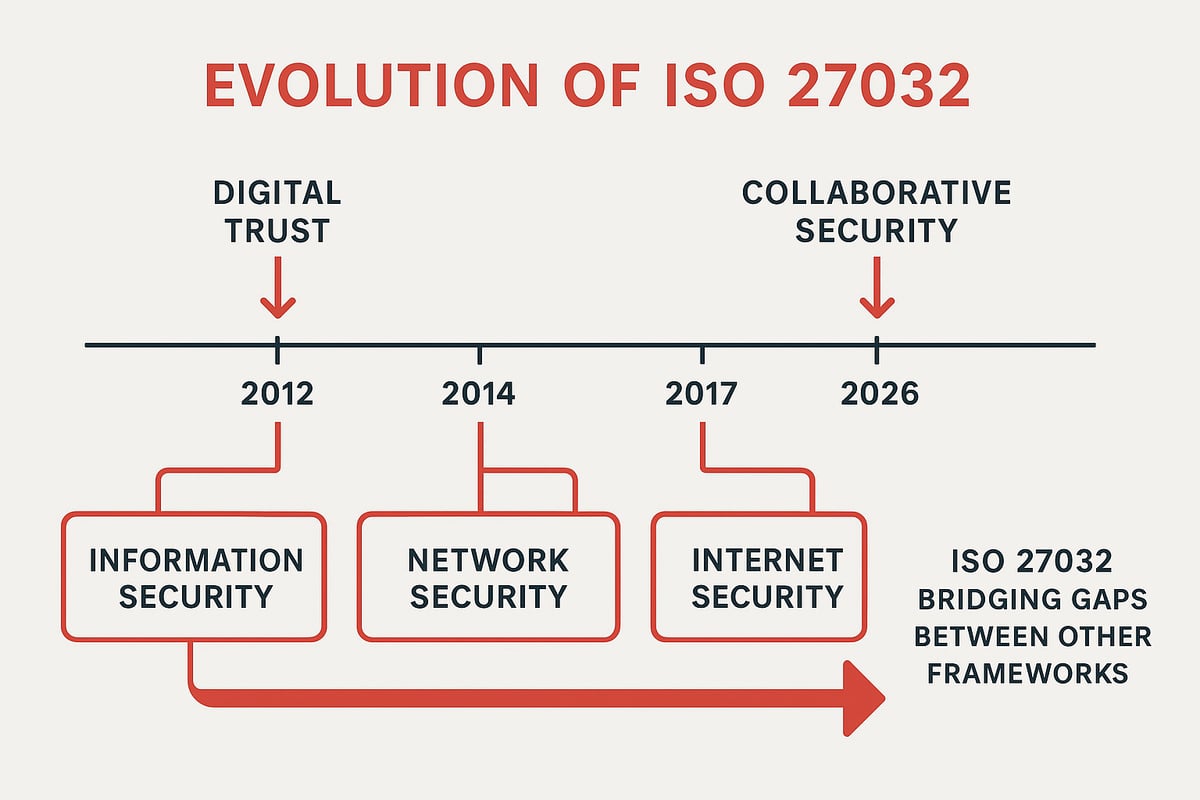
At its core, iso 27032 is designed to address security in cyberspace. Unlike traditional information security standards, it looks beyond the boundaries of a single organization and emphasizes the importance of digital trust and collaborative security. The standard recognizes that in 2026, no business operates in isolation. Supply chains, third-party vendors, and remote teams all share the responsibility for a secure digital environment.
What sets iso 27032 apart from other frameworks? While ISO 27001 focuses on establishing an Information Security Management System (ISMS) and ISO 27002 offers detailed controls, iso 27032 zeroes in on cyberspace and the relationships between interconnected systems. It also complements frameworks like the NIST Cybersecurity Framework, filling gaps where traditional standards may not address real-world cyber risks.
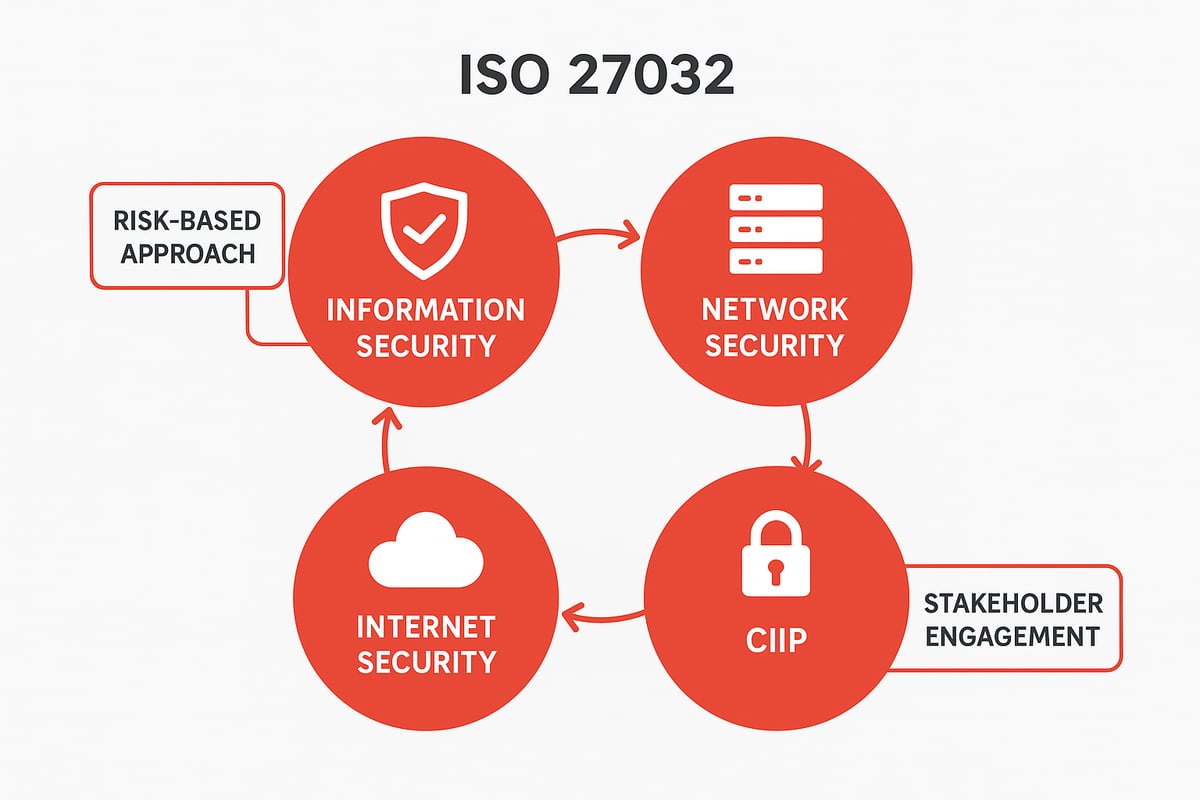
The four domains at the heart of iso 27032 are:
- Information security: Protecting data from unauthorized access or alteration.
- Network security: Securing network infrastructure and preventing unauthorized intrusion.
- Internet security: Safeguarding online assets, including web applications and cloud services.
- Critical information infrastructure protection (CIIP): Defending essential systems that underpin business operations.
As digital transformation accelerates, the relevance of iso 27032 grows. Remote work and cloud adoption have made organizations more vulnerable, exposing new entry points for cybercriminals. Recent studies show cybercrime remains a top business risk, with attacks increasing by over 20% in the past two years. Competitor data suggests organizations without comprehensive cyber frameworks are 40% more likely to experience significant breaches.
Consider the high-profile ransomware attacks and supply chain breaches that have made headlines in recent years. Many of these incidents could have been mitigated with iso 27032 controls, such as robust network monitoring and enforced collaborative policies across business partners.
Where iso 27032 truly shines is in its ability to bridge the gap between theory and practice. By offering practical guidance for building digital trust and fostering collaboration, it helps organizations translate abstract security goals into real-world results. As we move further into 2026, organizations that align with iso 27032 will be better equipped to manage threats, protect their assets, and build lasting trust with customers and partners.
Key Principles and Controls of ISO 27032
As organizations face an ever-changing digital threat landscape, understanding the key principles and controls of iso 27032 is essential for building resilience. This section explores the guiding values, technical safeguards, and implementation steps that help teams align with the standard and stay ahead of cyber risks.
Core Cybersecurity Principles
At the heart of iso 27032 is a strong focus on a risk-based approach. This means organizations identify, assess, and prioritize threats based on their likelihood and impact, rather than trying to defend against everything at once.
Collaboration is another pillar. Iso 27032 encourages organizations to break down silos and engage all stakeholders, from IT teams to business units and even third-party vendors. This shared responsibility ensures that everyone contributes to reducing cyber risk.
The standard also aligns with broader information security management systems, weaving its principles into existing frameworks. For example, cross-functional teams can work together to spot vulnerabilities across departments, shrinking the attack surface.
Why do these principles matter so much in 2026? As cyber threats grow more sophisticated, no single team can tackle them alone. By uniting around the iso 27032 philosophy, organizations create a culture where everyone plays a part in defense.
Technical Controls and Best Practices
Iso 27032 sets out a range of technical controls that help organizations stay resilient against cyber threats. Secure coding practices are a foundation, preventing vulnerabilities right from the start of software development.
Network monitoring plays a vital role. Continuous monitoring helps detect and respond to threats like DDoS attacks or exploits before they escalate. Server and application controls—such as strong authentication, encryption, and configuration management—add layers of defense.
End-user workstation controls are equally important. Regular training, up-to-date endpoint protection, and ongoing awareness campaigns help staff recognize and avoid phishing or social engineering attempts.
Here are some practical examples:
- Deploying multi-factor authentication across critical systems
- Encrypting sensitive data at rest and in transit
- Running regular phishing simulations to test user awareness
Organizations with robust iso 27032 controls respond to incidents faster and recover with less disruption. This agility is crucial in today’s fast-paced, cloud-centric world.
As we look ahead to 2026, integrating these technical safeguards is not just about compliance—it’s about building muscle memory for cyber resilience. The iso 27032 approach helps teams adapt quickly as new threats emerge.
Implementation Guidance and Documentation
Putting iso 27032 into action starts with integrating its controls alongside existing frameworks like ISO 27001. Begin by developing clear policies that reflect your organization’s unique risks and needs.
Risk assessment is a critical step in this journey. By mapping iso 27032 controls to specific threats and vulnerabilities, organizations can focus resources where they matter most. For a deeper dive into practical risk assessment strategies, check out this risk assessment in cybersecurity resource.
Documentation is more than a formality—it is vital for accountability and continuous improvement. Use templates and checklists to capture key decisions, roles, and controls. Automation tools can help streamline monitoring and reporting, freeing up time for strategic work.
Continuous improvement cycles keep your security posture strong. Regularly review policies, run incident response exercises, and update controls as technologies and threats evolve.
By following iso 27032 implementation guidance, organizations build a living, breathing defense system that adapts to the real world. The journey is ongoing, but with the right steps, every organization can become more cyber resilient.
ISO 27032 vs. ISO 27001: Complementary Standards Explained
In today’s threat landscape, understanding the relationship between iso 27032 and ISO 27001 is essential for any organization aiming to build a truly resilient cybersecurity posture. Both standards are influential, yet they serve distinct and complementary purposes.
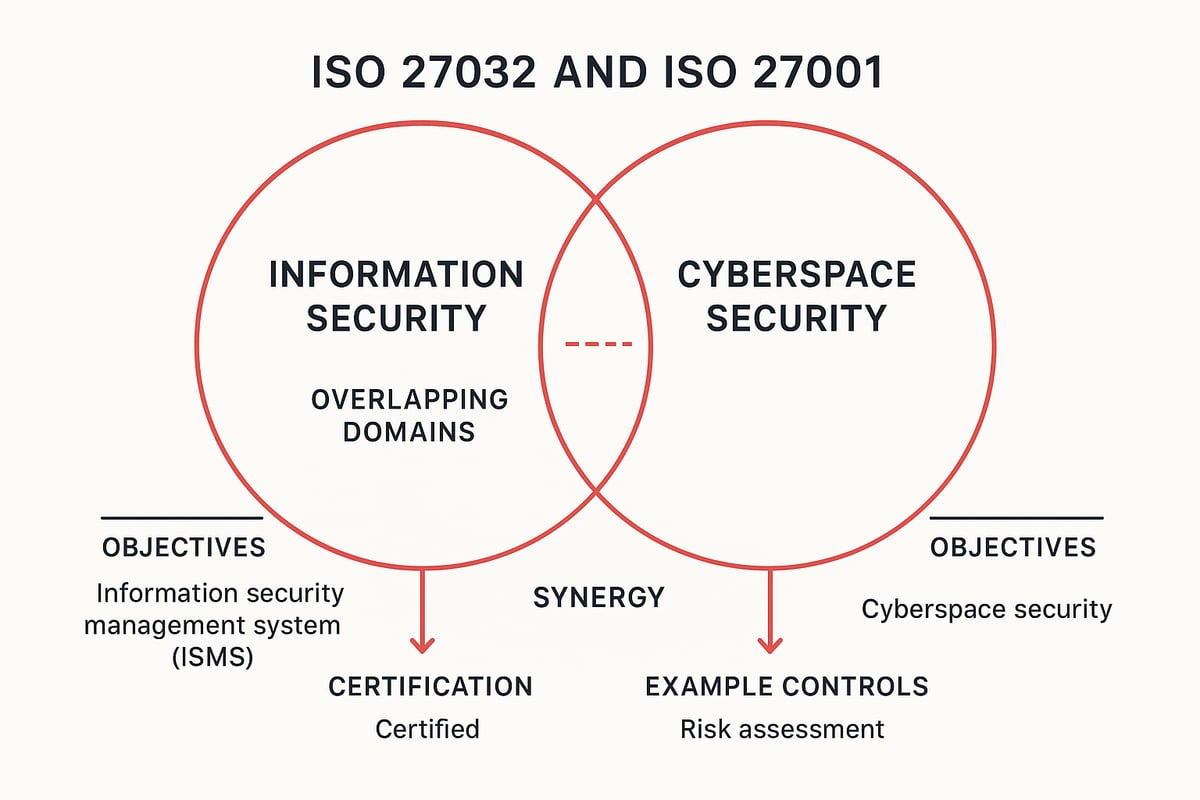
Let’s start by clarifying their core objectives. ISO 27001 is designed as a certifiable framework for implementing an Information Security Management System (ISMS). It focuses on protecting organizational data through systematic processes, risk management, and continual improvement. In contrast, iso 27032 provides practical guidelines for securing cyberspace, with a focus on digital trust, collaborative security, and addressing threats specific to the digital ecosystem.
A key distinction is that ISO 27001 leads to formal certification, offering organizations a recognized badge of information security excellence. This certification is often required for regulatory compliance or business partnerships. On the other hand, iso 27032 is advisory in nature, meaning it offers guidance but does not result in a formal certification. Instead, it fills critical gaps by addressing emerging cyber risks like phishing, social engineering, and cloud vulnerabilities that may not be fully covered by traditional ISMS frameworks.
The real power comes from combining both standards for a layered defense. For example, organizations can use iso 27032 to enhance incident response, secure cloud environments, and foster collaboration across departments and with external partners. At the same time, ISO 27001 provides the backbone for managing information security processes. Mapping controls between the two can reveal valuable synergies. For instance, aligning password management policies or incident response procedures ensures both cyberspace and information assets are well protected.
To see how iso 27032 fits within a broader security approach, explore this Cybersecurity frameworks overview, which highlights how multiple standards can work together for comprehensive protection.
It’s important to communicate the value of implementing both standards to leadership and stakeholders. Relying solely on ISO 27001 may leave gaps in cyber resilience, especially as threats grow more complex. By integrating iso 27032, organizations demonstrate proactive risk management and a commitment to digital trust, building confidence among customers, partners, and regulators. Ultimately, this dual approach supports stronger, future-proofed security in an ever-changing digital world.
Step-by-Step Guide: Implementing ISO 27032 in 2026
Embarking on your iso 27032 journey can feel overwhelming, but breaking it into manageable steps empowers your team and builds confidence. Let’s walk through a practical, six-step approach to help your organization implement iso 27032 effectively in 2026.
Step 1: Assess Current Cybersecurity Posture
Start with a thorough self-assessment. Compare your current security controls against iso 27032 recommendations. Identify your most critical assets, potential threats, and existing vulnerabilities.
Use a risk assessment template to structure your findings. Many organizations benefit from external frameworks that align with iso 27032, such as the AssessITS: IT and Cybersecurity Risk Assessment Framework, which can help you prioritize and document risks clearly.
List the top five risks to your business and note where your current practices fall short. This honest evaluation is the foundation for everything that follows.
Step 2: Engage Stakeholders and Build a Collaborative Team
Cybersecurity is a team sport. Bring together IT, business units, HR, legal, and even trusted vendors to form a cross-functional group. Each perspective is valuable for iso 27032 implementation.
Host interactive workshops to build a shared understanding of threats and responsibilities. Encourage open dialogue about past incidents and future concerns.
When everyone feels heard and invested, your security culture grows stronger and more resilient. This collaborative approach reduces the risk of gaps in your iso 27032 strategy.
Step 3: Develop and Update Cybersecurity Policies
Draft or update policies that specifically address the core domains of iso 27032, such as network security, internet use, and critical infrastructure protection.
Integrate these policies with your existing information security management systems. Use policy templates for areas like secure software development or network monitoring to save time and ensure consistency.
Review policies with your team and make sure they are clear, concise, and actionable. Well-defined policies lay the groundwork for effective iso 27032 control deployment and future audits.
Step 4: Deploy Technical and Organizational Controls
Now it’s time to put your plans into action. Implement technical safeguards recommended in iso 27032, such as strong authentication, robust encryption, and continuous network monitoring.
Launch end-user awareness programs to educate staff about phishing, password hygiene, and reporting suspicious activity. Consider rolling out simulations and endpoint protection tools to reinforce learning.
When controls are layered both technically and organizationally, your organization is better prepared to detect and respond to cyber threats under iso 27032.
Step 5: Monitor, Review, and Continuously Improve
Establish real-time monitoring and incident response protocols to catch threats early. Regularly review your iso 27032 controls and update them as new risks emerge or technologies evolve.
Automate log analysis and threat detection where possible. Schedule periodic tabletop exercises to test your response plans.
Continuous improvement is a core principle of iso 27032. By making reviews routine, you foster agility and readiness in your security posture.
Step 6: Document and Report Progress
Keep detailed records of your iso 27032 implementation process, from risk assessments to control deployments and incident responses. This documentation is critical for demonstrating compliance and measuring improvement over time.
Prepare regular reports for leadership and stakeholders. Use dashboards to visualize key metrics like incident response times and risk reduction.
Sharing progress builds trust and ensures accountability. Over time, your documented efforts will become a roadmap for future iso 27032 enhancements, helping your organization stay resilient and proactive.
The Business Impact: Benefits and ROI of ISO 27032 Adoption
Facing an ever-shifting cyber threat landscape, organizations must act decisively to protect their digital assets. Adopting iso 27032 is a strategic move that directly reduces cyber risk and shields sensitive data. By implementing the standard’s controls, companies can proactively identify and manage vulnerabilities, closing common gaps exploited by attackers.
Reducing Cyber Risk with ISO 27032
Implementing iso 27032 equips organizations with a robust framework to tackle evolving threats head-on. This standard guides teams to prioritize assets, assess risks, and deploy targeted defenses against ransomware, phishing, and insider attacks.
For many companies, iso 27032 fills critical gaps not addressed by traditional IT controls. By focusing on cyberspace-specific risks, it helps organizations prevent incidents before they escalate. According to recent industry data, businesses with structured cybersecurity programs see up to 50 percent fewer major breaches compared to those without such measures.
Building Trust and Meeting Compliance
In today’s digital economy, trust is everything. Demonstrating adherence to iso 27032 reassures stakeholders that security is taken seriously. Customers, partners, and regulators look for evidence of proactive cyber risk management.
Adoption of iso 27032 also supports compliance with regulations like GDPR, NIS2, and DORA by addressing cyber-specific requirements. For a deeper understanding of foundational concepts underpinning these practices, you can explore Information and cyber security basics. This commitment not only reduces legal exposure but also strengthens your brand’s reputation.
Faster Recovery and Resilience
When incidents do occur, iso 27032 ensures your organization is ready to respond and recover. Structured response plans, regular drills, and clear communication channels minimize downtime and financial losses.
Competitor analysis shows that businesses with robust cyber frameworks recover faster and face fewer legal penalties after a breach. For example, organizations leveraging iso 27032 controls have reported resuming normal operations 30 percent faster than those relying on ad hoc processes.
Fostering a Security-Aware Culture
The benefits of iso 27032 go beyond technology—they help build a culture of security awareness. Regular training, clear policies, and open communication empower everyone to play a role in protecting the organization.
Consider a case where a mid-sized enterprise adopted iso 27032, rolled out new awareness campaigns, and saw phishing click rates drop by half within six months. This investment pays off in resilience, customer confidence, and long-term business continuity. Ultimately, embracing iso 27032 is not just about compliance—it is a proactive strategy for securing your future.
Practical Resources, Expert Insights, and Next Steps for Cyber Leaders
Navigating the complexities of iso 27032 implementation can feel overwhelming, but the right resources and expert advice can make all the difference. Let’s explore practical tools, lessons from seasoned cyber leaders, and your next steps for building a resilient security program.
Tools, Templates, and Checklists for Implementation
Starting your iso 27032 journey is easier when you have access to proven tools. Publicly available resources like policy templates, risk assessment checklists, and incident response forms can streamline your process. These documents help ensure you’re covering all essential iso 27032 domains from network security to critical information infrastructure protection.
Automation platforms can further simplify compliance tracking, document management, and reporting. Many organizations rely on digital checklists to verify that each iso 27032 control is properly deployed and monitored. For a deeper dive into recent updates and actionable controls, the article on Key Changes in ISO/IEC 27032:2023 can provide valuable context as you select your tools.
Building your toolkit early sets you up for success and gives your team confidence as you move forward.
Expert Perspectives: Real-World Lessons from Cybersecurity Leaders
Learning from those who have championed iso 27032 in the field is invaluable. CISOs and practitioners emphasize that technical controls alone are not enough—building a culture of security is just as critical. One lesson often shared is the importance of cross-functional collaboration. When IT, HR, and business units join forces, iso 27032 adoption accelerates and risks are reduced.
Experts also note that failed implementations usually stem from poor communication or lack of leadership buy-in. Successful teams create regular opportunities for feedback, training, and shared learning. For practical advice on aligning leadership and governance with iso 27032, many leaders reference resources like Security governance best practices. These insights can help you avoid common pitfalls and foster a resilient security culture.
LarsBirkeland.com: Strategic Guidance for Cybersecurity Leaders
LarsBirkeland.com is a trusted partner for anyone tackling iso 27032. The platform offers step-by-step guides, ready-to-use templates, and access to the exclusive CISO LaunchPad Community. These resources empower IT leaders and CISOs to translate iso 27032 principles into practical strategies that fit their unique environments.
What sets LarsBirkeland.com apart is its focus on real-world frameworks, actionable checklists, and a supportive peer network. Whether you need help mapping iso 27032 controls or want to connect with other cyber leaders, this community has you covered. It’s a space where strategic insights meet day-to-day solutions, helping you future-proof your organization and inspire your team.
Staying Ahead: Continuous Improvement and Future-Proofing
The journey with iso 27032 does not end after initial implementation. Ongoing training, regular process reviews, and staying alert to new threats are vital for lasting success. Organizations that prioritize continuous improvement—by subscribing to security updates, joining professional communities, and scheduling framework reviews—consistently maintain stronger cyber defenses.
As cyber risks evolve, so should your approach. Leverage your network for shared learning and keep up with revisions to iso 27032 and other standards. Remember, two mentions of iso 27032 in this section drive home the point: it is not just a standard, but a living guide for your security journey.
By embracing continuous improvement and staying connected, you set your organization up for long-term resilience and confidence.
We’ve covered a lot together—from making sense of ISO 27032’s practical steps to building a stronger security culture that really lasts. If you’re ready to go even further, you don’t have to do it alone. I believe in learning from real-world experiences, sharing insights, and supporting each other through every cybersecurity challenge.
That’s why I invite you to connect with peers, swap ideas, and get the encouragement you need as you lead your organization forward. Let’s keep growing together, Join Cyber Launchpad Community and be part of a group that truly gets it.