In 2026, cyber attacks are making headlines almost every week. The average cost of a data breach keeps climbing, and organizations around the globe are feeling the pressure. Cyber risk assessment is no longer optional—it is a vital part of every business strategy.
Threats have grown more complex and more personal, targeting not just systems but the very heart of your business. We all need clear, practical guidance to stay ahead.
This guide will walk you through the essentials of cyber risk assessment, from definitions and frameworks to proven methods and future trends. You will discover actionable steps and real-world advice to help protect your organization, build resilience, and communicate risk with confidence.
Understanding Cyber Risk Assessment: Definitions and Core Concepts
In today’s digital world, a strong understanding of cyber risk assessment is essential for every organization. Let’s break down the basics together, so you’ll feel empowered to make informed decisions about your security posture.
What is a Cyber Risk Assessment?
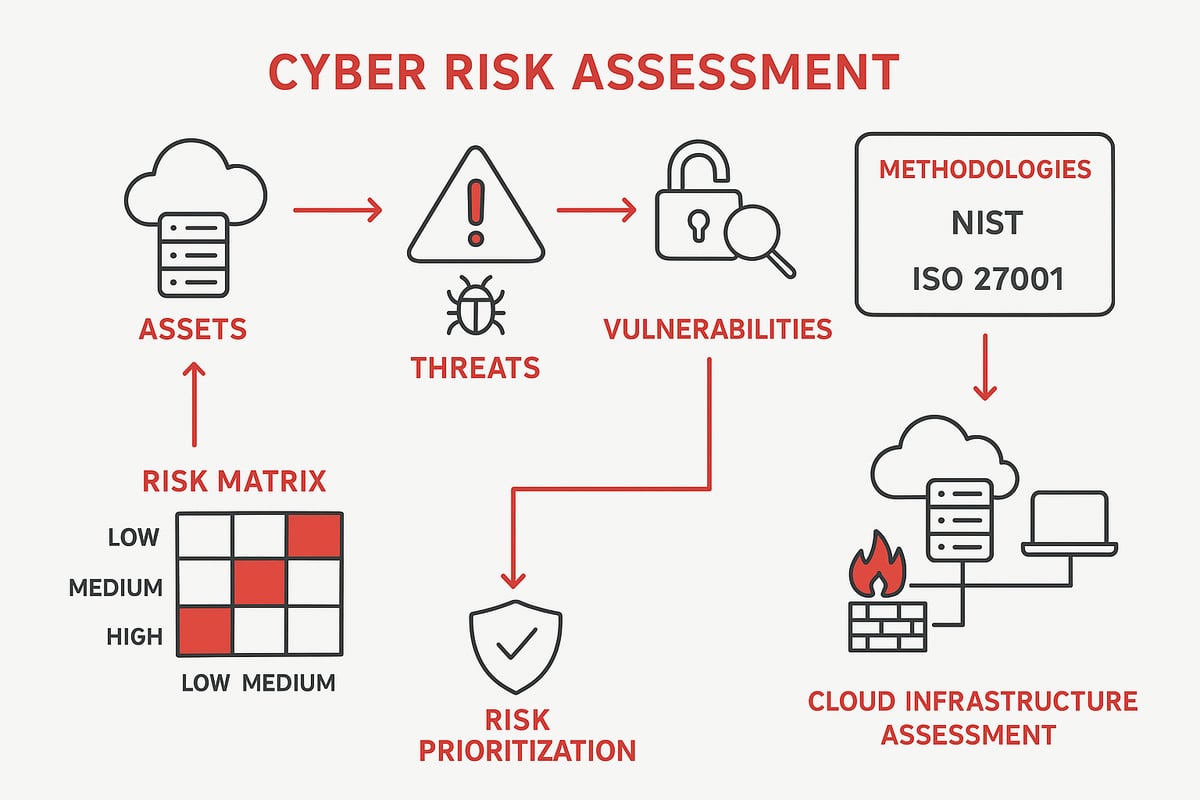
A cyber risk assessment is a structured process that helps organizations identify, evaluate, and prioritize threats and vulnerabilities within their IT environments. By focusing on protecting sensitive data, information systems, and business-critical assets, this process forms the backbone of any modern cybersecurity program.
Cyber risk assessment uses established frameworks, such as NIST and ISO 27001, to ensure consistency and thoroughness. For example, when a business launches a new AI-driven unit in the cloud, a cyber risk assessment helps pinpoint security gaps before attackers can exploit them.
This foundational step empowers organizations to proactively safeguard what matters most.
Why Cyber Risk Assessment Matters in 2026
Cyber risk assessment is vital in 2026 because the stakes have never been higher. The average cost of a data breach soared to $4.88 million in 2024, reminding us how costly inaction can be. As companies rely more on AI and cloud services, exposure to new risks grows.
Alarmingly, only 24 percent of generative AI initiatives were secured in 2024, according to IBM. Proactive cyber risk assessment enables early identification of threats, giving organizations a crucial advantage. Stringent regulations like GDPR, HIPAA, and PCI DSS also demand a documented approach to risk.
Staying ahead means making assessment a top priority.
Key Elements and Terminology
Understanding cyber risk assessment means getting familiar with some essential terms:
- Critical assets: Data, applications, or systems vital to your organization.
- Threat vectors: Paths attackers use, such as malware or phishing.
- Vulnerabilities: Weak spots like unpatched software or weak passwords.
- Risk matrix: A tool to map the likelihood and impact of risks.
It’s important to distinguish between threats (like insider attacks or natural disasters) and vulnerabilities (like misconfigurations). Risk calculation blends likelihood with impact, while risk appetite and tolerance guide decision-making.
Mastering these concepts lays the groundwork for an effective assessment.
Common Methodologies and Frameworks
Organizations rely on proven frameworks to ensure their cyber risk assessment is thorough and repeatable. The NIST Cybersecurity Framework is a popular choice, offering a structured approach that’s widely adopted. ISO/IEC 27001 provides an international standard for information security management, while custom frameworks address unique industry needs.
Tools like MITRE ATT&CK help map threats to real-world tactics. Consistency is key—repeatable, auditable processes build trust and resilience. For a deeper dive into foundational knowledge and assessment methodologies, explore risk assessment in cybersecurity.
By choosing the right framework, organizations set themselves up for ongoing success.
The Evolving Threat Landscape: Trends and Challenges for 2026
The digital world in 2026 is more unpredictable than ever. Organizations face a wave of new risks each day. To stay ahead, a strong cyber risk assessment is no longer optional but essential. Let’s explore the trends and challenges shaping this landscape.
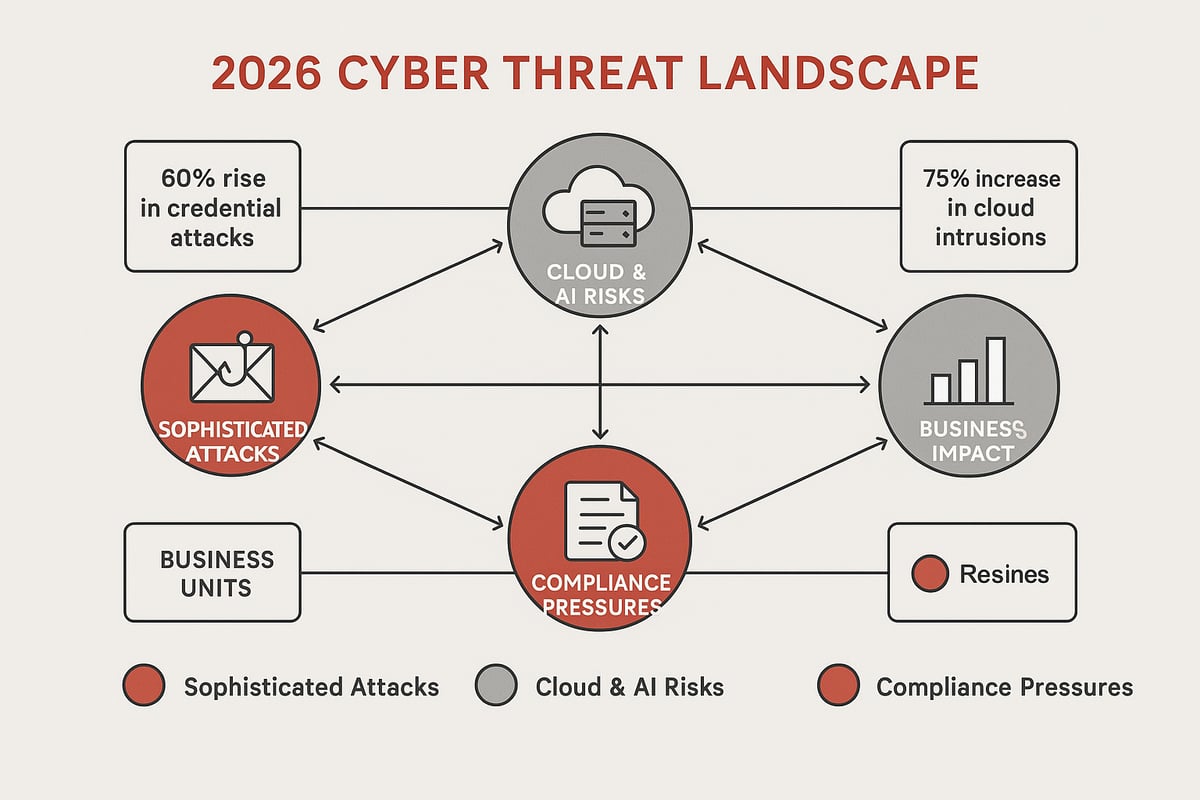
Rise of Sophisticated Cyberattacks
In 2026, attackers use smarter tactics to breach defenses. “Hands-on” attacks, like credential phishing and social engineering, rose 60% last year. Instead of brute force, threat actors now target users and exploit trusted accounts for stealthy access.
This shift means that cyber risk assessment must evolve too. Modern attacks bypass traditional security, making it crucial to identify gaps and anticipate new techniques. For example, AI-powered attacks can quickly adapt, putting sensitive business systems at greater risk.
Organizations that proactively update their cyber risk assessment process are better equipped to spot and stop these advanced threats before they cause harm.
Cloud and AI Security Risks
Cloud adoption and AI are transforming how we work, but they bring new risks. Last year, cloud intrusions jumped by 75%. Attackers are not just targeting cloud data, but also the AI systems driving business automation.
AI is a double-edged sword: it can defend, but also be used by adversaries to find weaknesses. As these technologies grow, integrating cloud and AI into your cyber risk assessment is a must. For more on how AI is reshaping risk analysis, see this AI in cybersecurity risk assessment guide.
By proactively assessing these emerging risks, organizations can secure innovation without sacrificing safety.
Regulatory and Compliance Pressures
Regulatory demands are tightening across the globe. New privacy laws like GDPR and CCPA now reach more regions and industries. Sector-specific rules, such as PCI DSS for finance or HIPAA for healthcare, add extra layers of complexity.
Non-compliance has real consequences: hefty fines and damage to your reputation. Recent penalties for mishandling data show regulators are serious. A robust cyber risk assessment helps organizations stay ahead, ensuring they meet legal obligations and avoid costly setbacks.
Staying compliant is not just about ticking boxes. It builds trust with customers and partners, strengthening your organization’s standing.
Business Impact and Risk Perception
Cyber threats are now a top business concern, not just an IT issue. Downtime, data loss, and operational disruptions can halt business in an instant. Boards and executives are demanding clear reporting on cyber risk assessment outcomes.
Expectations have shifted. Transparent communication, regular risk reviews, and alignment with business goals are now standard. Insurers also scrutinize cyber defenses more closely, requiring detailed documentation before providing coverage.
When organizations embed cyber risk assessment into decision-making, they protect not only data, but their reputation and future success.
Step-by-Step Cyber Risk Assessment Process for 2026
Navigating the cyber risk assessment process in 2026 requires clarity, collaboration, and a structured approach. Each step builds a stronger, more resilient security posture for your organization. Whether you are new to cyber risk assessment or refining a mature program, following these steps will help you stay proactive and confident.
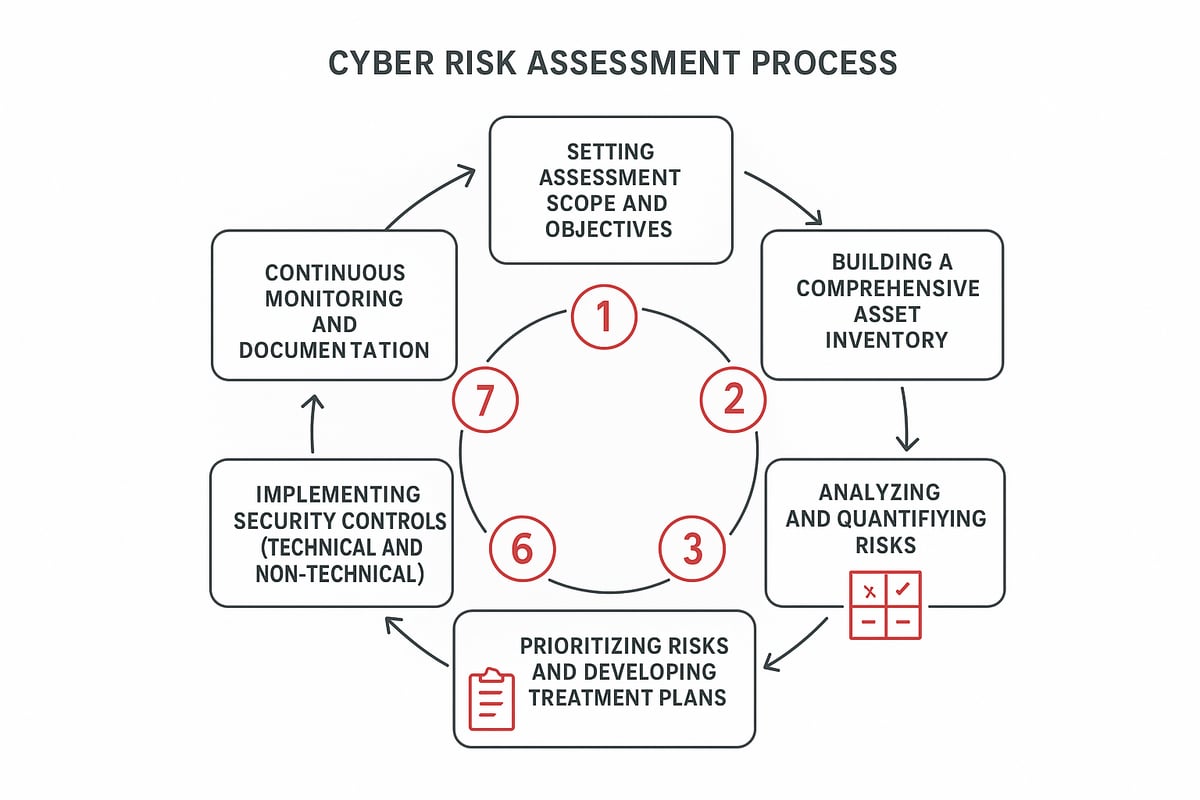
Step 1: Define Scope and Objectives
Every effective cyber risk assessment starts with clear direction. Begin by setting assessment goals, such as reducing risk, ensuring compliance, or optimizing resources. Define what you want to protect—this might include the entire organization, a specific business unit, or only critical cloud systems.
Involve key stakeholders from IT, security, compliance, and business leadership. Their input ensures that the cyber risk assessment aligns with real-world priorities and gets executive buy-in. For example, after migrating to the cloud, you may focus your assessment on new cloud environments and the data they house.
Establishing a defined scope keeps the process manageable and ensures that results are meaningful. Remember, a well-scoped cyber risk assessment is the foundation for actionable insights. Clear objectives help everyone stay motivated and engaged throughout the journey.
Step 2: Build a Comprehensive Asset Inventory
A thorough asset inventory is at the heart of any successful cyber risk assessment. Start by auditing all hardware, software, cloud platforms, and data repositories. Do not overlook remote devices or SaaS applications, as they are often overlooked entry points.
Classify each asset by value, sensitivity, and regulatory importance. This allows you to focus the cyber risk assessment on what matters most. Visualizing your network architecture helps pinpoint potential vulnerabilities and areas where threats could emerge.
Consider leveraging automated tools for real-time asset discovery. For more guidance, check out Cyber risk assessment tools, which can accelerate and enhance your inventory process. A detailed inventory empowers you to spot gaps before attackers do.
Step 3: Identify Threats and Vulnerabilities
With your assets mapped, the next step in cyber risk assessment is identifying internal and external threats. Catalog risks like malware, phishing, insider actions, and natural disasters. Then, assess vulnerabilities—misconfigured cloud settings, unpatched software, or weak credentials.
Leverage established frameworks such as MITRE ATT&CK and the National Vulnerability Database to ensure comprehensive coverage. For instance, discovering unprotected admin interfaces in cloud applications highlights areas needing urgent attention.
This step is crucial because it links your digital landscape to real-world attack scenarios. The more thorough your threat and vulnerability identification, the more effective your cyber risk assessment will be in guiding mitigation efforts.
Step 4: Analyze and Quantify Risks
Now, it is time to make your cyber risk assessment actionable. Use a risk matrix to map the likelihood and impact of each threat exploiting a vulnerability. Consider factors like how easy a threat is to discover, exploit, and repeat.
Quantify risks in business terms—think financial loss, operational disruption, and regulatory penalties. For example, calculate the potential impact of a ransomware attack on sensitive customer data. This approach helps prioritize mitigation efforts where they matter most.
Involving business leaders in this analysis ensures that risk ratings reflect both technical and operational realities. The clearer the quantification, the more persuasive your cyber risk assessment will be to decision-makers.
Step 5: Prioritize Risks and Develop Treatment Plans
After quantifying risks, the next step in cyber risk assessment is prioritization. Rank risks based on business impact, likelihood, and the cost-benefit of mitigation. Focus on those that could cause the most harm or are easiest for attackers to exploit.
Develop treatment plans for each high-priority risk. Strategies may include preventive, detective, or corrective controls. Take into account your organization’s risk appetite and available resources. For example, if you see a spike in credential-based attacks, prioritize identity controls like multi-factor authentication.
Collaboration is key here—bring together IT, security, and business stakeholders to ensure treatment plans are practical and aligned with core objectives.
Step 6: Implement Security Controls
Once you have a prioritized list, it is time to implement controls. In your cyber risk assessment, this means deploying technical solutions like firewalls, encryption, endpoint detection and response, and multi-factor authentication.
Do not forget non-technical controls—policies, awareness training, and even physical security play a role. Ensure that all controls are configured to address the specific risks identified earlier. For example, roll out zero trust access models to protect remote workers and sensitive cloud resources.
Integration and alignment are vital. Controls should work together to create overlapping layers of defense, reducing gaps and making it harder for attackers to succeed.
Step 7: Monitor, Review, and Document
The cyber risk assessment process is not a one-time event. Set up continuous monitoring with SIEM platforms, threat intelligence feeds, and regular audits. Document all findings, risk scenarios, and remediation actions in a risk register.
Conduct quarterly reviews or respond promptly to new threats and changes in your environment. Keep stakeholders informed with clear, concise updates. This ongoing cycle strengthens your security posture and ensures your cyber risk assessment stays relevant.
Documentation and communication are just as important as technical controls. They help build trust, demonstrate compliance, and create a culture of shared responsibility.
Advanced Risk Assessment Frameworks and Tools
Staying ahead in cyber risk assessment means understanding both the frameworks that guide us and the cutting-edge tools that make our work more effective. Let’s explore how the right combination of structure and technology can help us build robust, repeatable security programs.
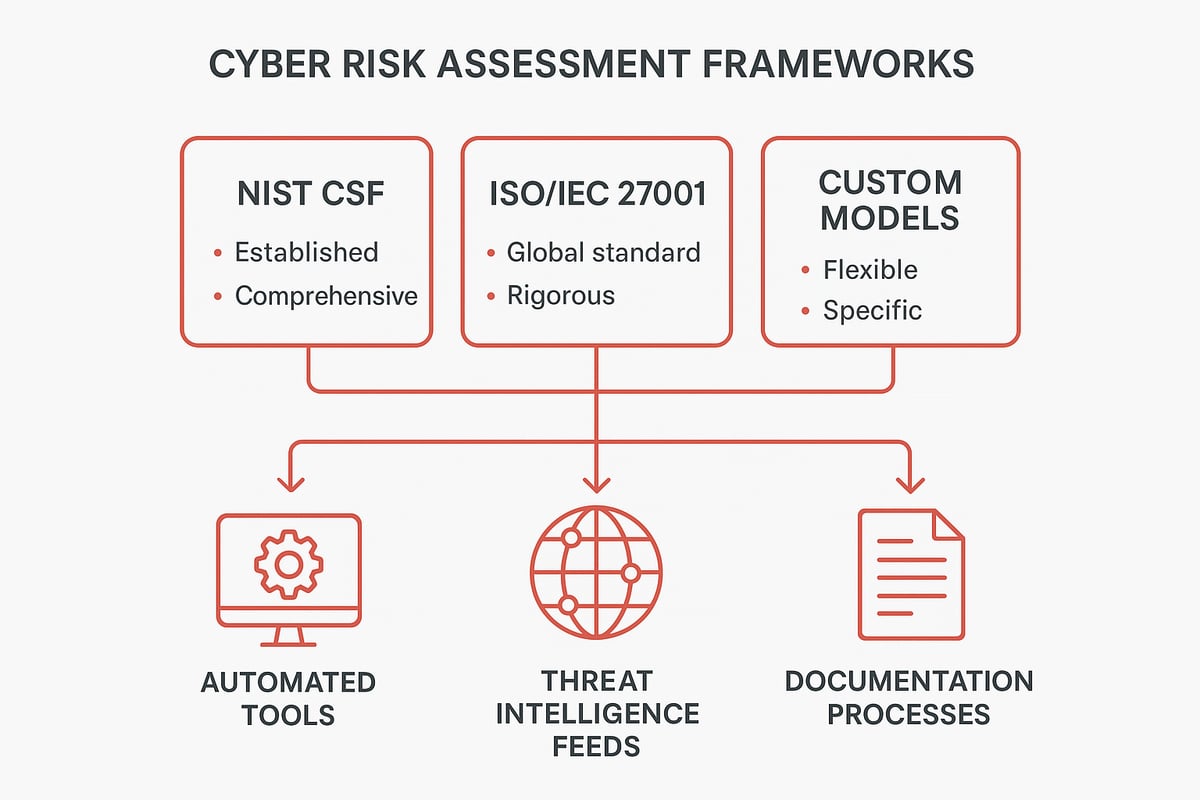
Comparing Leading Frameworks: NIST, ISO, and Custom Models
Choosing the right framework is foundational for a successful cyber risk assessment. The NIST Cybersecurity Framework Overview is popular for its flexibility and global recognition, making it a go-to for many organizations. ISO/IEC 27001 stands out for its strict international compliance requirements, especially in regulated industries.
Custom models are often adopted by sectors with unique needs, such as finance or healthcare. While NIST is praised for its adaptability, ISO/IEC 27001 ensures rigorous process discipline. Hybrid approaches are gaining traction, particularly for multinational companies that must balance local and global requirements.
Key Tools and Technologies for 2026
Modern cyber risk assessment increasingly relies on advanced tools to keep pace with threats. Automated risk assessment platforms streamline asset discovery and vulnerability identification, reducing manual effort. AI and machine learning-driven scanners quickly analyze complex environments, flagging weaknesses that might otherwise go unnoticed.
Integration with cloud-native security solutions is essential as organizations shift workloads to the cloud. Exposure management platforms give real-time visibility into the attack surface, which is crucial for proactive defense. These innovations empower teams to focus on strategic improvements rather than routine tasks.
Integrating Threat Intelligence and Continuous Assessment
The threat landscape changes daily, so cyber risk assessment must be dynamic. Real-time threat intelligence feeds provide up-to-date information on emerging tactics and vulnerabilities. Continuous controls monitoring, as opposed to periodic reviews, helps organizations adapt quickly to new risks.
Platforms like XDR and SOAR automate detection and response, freeing up human resources for higher-level analysis. Dynamic risk scoring ensures that risks are prioritized as conditions evolve. This approach helps us stay resilient even as adversaries change their methods.
Building a Repeatable, Auditable Process
A successful cyber risk assessment program is consistent and transparent. Clear documentation standards, such as well-maintained risk registers and standardized reporting templates, make it easier to track progress and demonstrate due diligence.
Repeatable processes mean every team, no matter the location, follows the same steps and standards. Using playbooks for recurring assessments ensures nothing is missed and helps onboard new team members efficiently. Ultimately, this structure builds trust with stakeholders and strengthens our security culture.
Maximizing the Business Value of Cyber Risk Assessment
Unlocking the full potential of cyber risk assessment is about more than ticking boxes. When done right, it becomes a powerful driver for security, compliance, savings, and trust. Let’s explore how organizations in 2026 can turn these assessments into lasting business value.
Enhancing Security Posture and Resilience
A robust cyber risk assessment shines a light on your assets, identities, and applications. By mapping out what you have and where your weaknesses lie, you can spot and fix vulnerabilities before attackers do.
For example, a thorough assessment may reveal misconfigured cloud storage or risky admin accounts. Addressing these issues early prevents breaches and keeps your defenses strong.
This proactive approach means your team is ready to respond and recover quickly if an incident occurs. In 2026, resilience is not just about having tools, but about knowing exactly where to focus your protection.
Reducing Regulatory and Financial Risk
One of the biggest business benefits of cyber risk assessment is reducing the chance of costly fines or penalties. With privacy laws evolving, staying ahead of compliance requirements is essential.
Documented assessments show regulators and insurers that you are taking cyber risk seriously. According to the IBM Cost of a Data Breach Report 2024, the average breach cost hit $4.88 million, making proactive steps critical.
Aligning with frameworks like ISO/IEC 27001 further demonstrates diligence and helps avoid unnecessary losses. Every assessment is an investment in your organization’s financial health.
Optimizing Resources and Reducing Costs
Every organization wants to make the most of its resources. Cyber risk assessment helps you focus your security spend where it matters most.
Instead of spreading your budget thin, you can prioritize the highest-impact risks. Early detection and mitigation save money by avoiding expensive breaches or downtime.
For instance, after identifying low-value controls, you might reallocate staff or funds to address more urgent threats. This targeted strategy streamlines operations and maximizes ROI.
Strengthening Stakeholder Communication and Decision-Making
Clear, actionable insights from cyber risk assessment empower leaders to make confident choices. Boards and executives expect risk reports that translate technical findings into business language.
Using templates and frameworks, you can communicate risk tolerance and priorities effectively. For more strategies on this front, explore Cyber risk management strategies.
Open dialogue builds trust with stakeholders, regulators, and partners. When everyone understands the risks and the plan, your organization moves forward together with clarity and purpose.
Future Trends and Expert Recommendations for 2026
The world of cyber risk assessment is rapidly evolving, and staying ahead means understanding tomorrow’s trends today. As we look to 2026, several key shifts are shaping how organizations approach security, resilience, and compliance. Let’s explore the most important trends and actionable recommendations that can elevate your cyber risk assessment strategy.
AI and Automation in Risk Assessment
Artificial intelligence is transforming cyber risk assessment by automating asset discovery, vulnerability detection, and risk scoring. AI-powered tools sift through vast amounts of security data, detecting patterns and anomalies that might escape human analysts. These solutions can provide real-time insights, helping us identify threats before they escalate.
For example, AI models are now used to flag suspicious user behavior and automate responses to emerging threats. Integrating frameworks such as the MITRE ATT&CK Framework allows these tools to map adversary tactics and techniques, making your cyber risk assessment more precise and actionable.
By leveraging automation, we reduce manual workloads and enhance our ability to adapt to new attack vectors as they arise.
Zero Trust and Identity-Centric Security
Zero Trust is no longer a buzzword—it’s a foundational strategy for any cyber risk assessment. The focus has shifted from perimeter defenses to verifying every user, device, and application, regardless of location. Identity and access management are now central to reducing risk, especially as remote work and supply chain ecosystems expand.
Cyber risk assessment frameworks must now account for decentralized environments and evolving identity threats. Using resources like the MITRE ATT&CK Framework helps organizations pinpoint gaps in identity controls and proactively address vulnerabilities.
Adapting your cyber risk assessment to prioritize identity-centric controls will help safeguard critical assets in an increasingly interconnected world.
Regulatory Evolution and Globalization
The regulatory landscape is becoming more complex and global in scope. New data privacy laws and reporting requirements are emerging across regions, requiring organizations to rethink their cyber risk assessment processes. Compliance is no longer just about ticking boxes—it’s about demonstrating active risk management and transparency.
Adopting international standards such as ISO/IEC 27001 Information Security Management helps organizations create consistent, auditable processes across borders. By embedding these standards into your cyber risk assessment, you can better anticipate regulatory changes and reduce the risk of fines or reputational damage.
Staying proactive will keep your organization prepared for the next wave of compliance challenges.
Building a Culture of Cyber Risk Awareness
A resilient cyber program is built on more than just technology and policies—it thrives on a culture of awareness. Embedding cyber risk assessment into daily business processes empowers every employee to be a part of the defense strategy. Executive buy-in and ongoing training make risk management a shared responsibility.
Innovative approaches, such as gamified awareness campaigns, keep engagement high and learning memorable. Regular communication about risks and protective measures ensures that everyone understands their role in safeguarding the organization.
Fostering a culture of cyber risk awareness will turn your team into a united front against threats, strengthening your overall security posture.
We’ve covered a lot together—from understanding what cyber risk really means for your business in 2026 to practical steps you can use right away. If you’re ready to put these ideas into action and want to connect with others facing the same challenges, you don’t have to go it alone.
Let’s keep this conversation going and support each other as we build stronger, more resilient organizations.
I invite you to Join CISO Launchpad Community—a space where IT leaders and security professionals share real-world advice, ask questions, and help each other grow. We’re in this together!








