As we approach 2026, the complexity and frequency of security threats in network security are reaching all-time highs. Every day, attackers are finding new ways to breach defenses, making it harder for organizations to stay protected.
Understanding security threats in network security is now essential for every business and IT professional. The risks go beyond lost data, impacting reputation, customer trust, and business continuity.
This guide is here to help you navigate the ever-changing threat landscape. You’ll discover what these threats are, how they work, and the best ways to detect and prevent them. We’ll share real-world cases, practical strategies, and expert insights to empower you.
If you want to safeguard your data, protect your team, and secure your future, you’re in the right place. Let’s dive in together and build a safer tomorrow.
Understanding Network Security Threats in 2026
As we move closer to 2026, security threats in network security are growing more complex and persistent. These threats target everyone, from individuals to global enterprises. Attackers are no longer just lone hackers, but organized groups with advanced tools. Staying informed about these evolving risks is essential for all of us who want to protect our data and our organizations.
Defining Network Security Threats
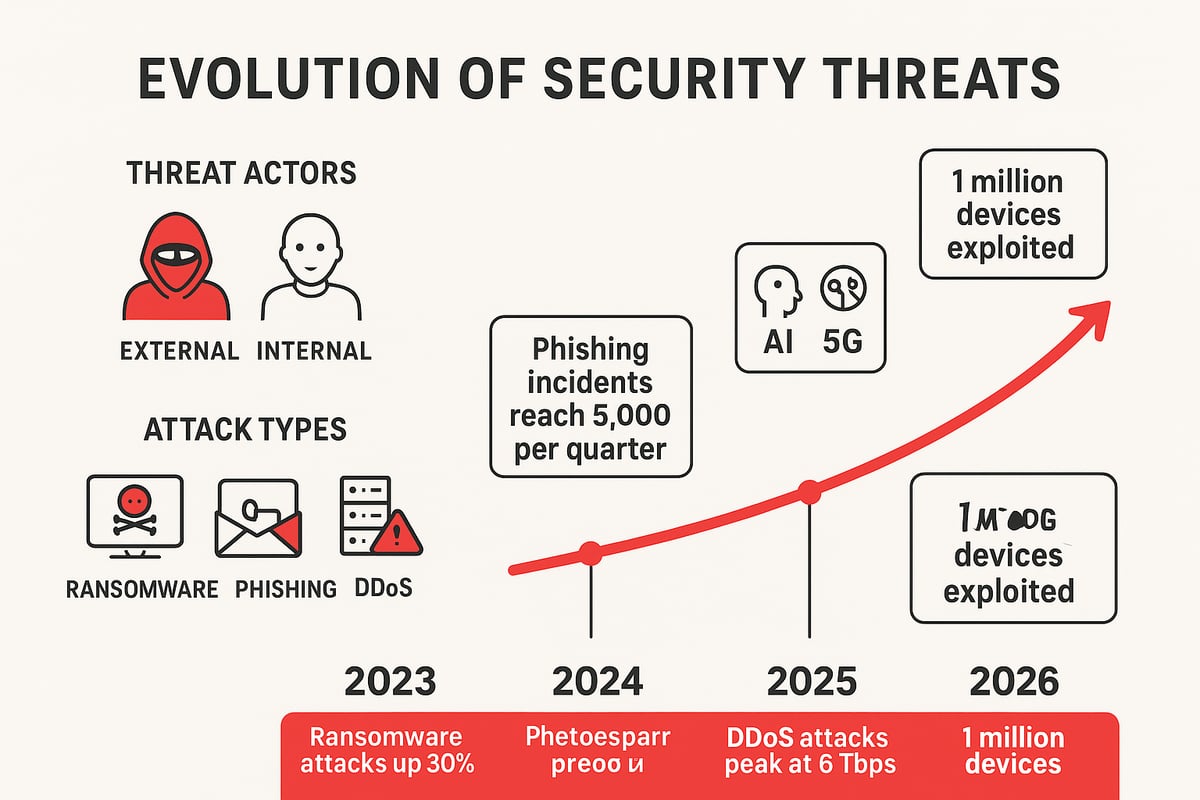
Security threats in network security include any malicious actions that aim to steal, alter, or disrupt sensitive information. These threats come from both outside attackers and insiders like employees or partners. Cybercriminals are using more advanced tactics, making it harder to spot and block attacks. In 2025, global cyber attacks surged by nearly 50 percent, with ransomware incidents rising 126 percent, according to the Global Cyber Attack Report. Common examples include ransomware, phishing, DDoS, and insider threats.
Evolution of Threats: 2023 to 2026
The landscape of security threats in network security has changed rapidly in recent years. New technologies like 5G, IoT, and AI have expanded both opportunities and risks. Attacks have shifted from random attempts to highly targeted, ongoing campaigns. Zero-day exploits and supply chain attacks are now more common, catching even prepared organizations off guard. Real-world incidents in 2024 and 2025 have shown how attackers can use weaknesses in interconnected systems to cause widespread harm.
Why Network Security Threats Matter
The consequences of security threats in network security can be severe for any organization. A single breach may lead to financial losses, damaged reputation, and legal trouble. Downtime from attacks can halt business operations, while regulatory penalties add to the burden. Human factors, such as social engineering and insider mistakes, play a big role too. On average, the cost and time needed to detect and respond to threats have both increased, highlighting the need for proactive defense and quick action.
Key Terminology and Concepts
Understanding key terms helps us navigate security threats in network security more confidently. Malware is software designed to harm. Ransomware locks files until a ransom is paid. Phishing tricks users into revealing secrets. DDoS overloads systems with traffic. Zero-day means attackers exploit unknown flaws. A threat actor is anyone behind an attack. Remember, threats are the dangers, vulnerabilities are the weaknesses, and risks are the potential impacts. Detection spots problems, prevention stops them, and response is how we recover.
Major Types of Security Threats in Network Security
Understanding the major types of security threats in network security is essential as we navigate the ever-changing digital landscape. Each threat brings unique challenges, and recognizing them early helps us build stronger defenses and protect what matters most.
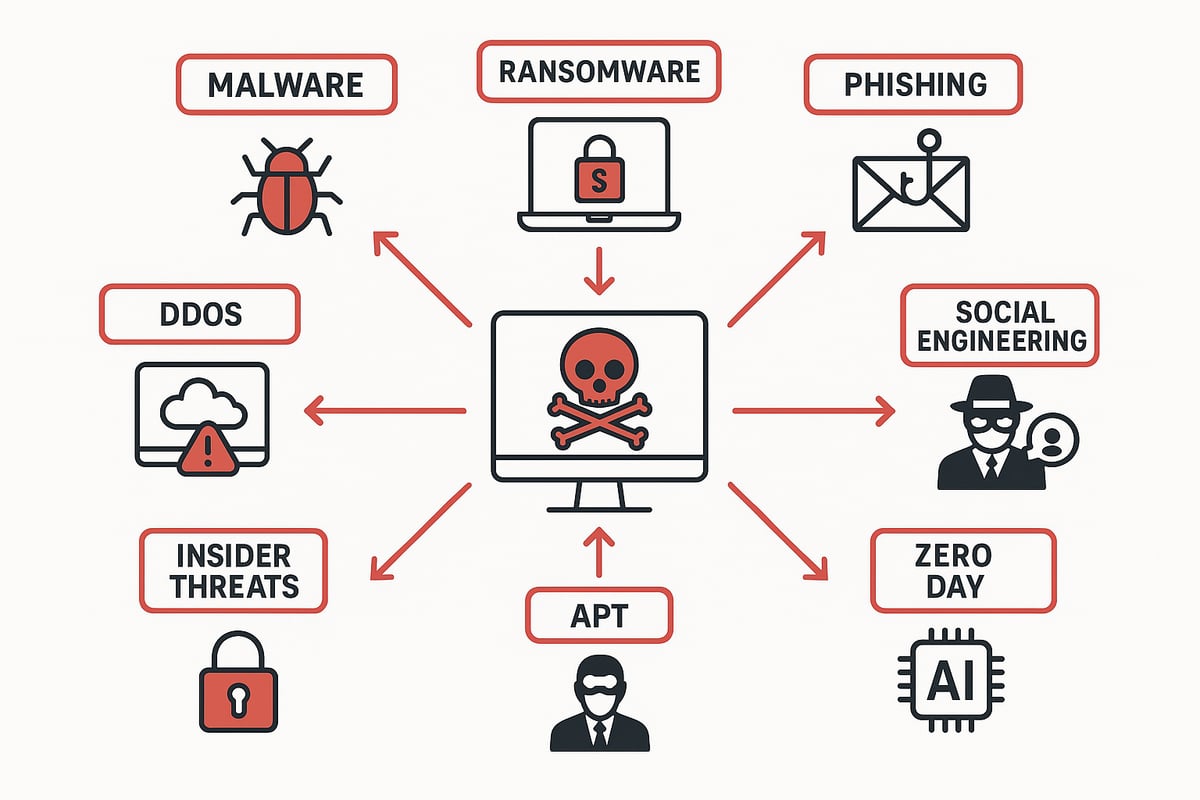
Malware and Ransomware
Malware and ransomware are two of the most persistent security threats in network security. Malware is any software designed to harm, steal, or disrupt, while ransomware specifically locks files or systems until a ransom is paid. Attackers often use phishing emails, malicious attachments, drive-by downloads, or compromised websites as infection vectors.
Recently, ransomware attacks have surged, with double extortion tactics and focused attacks on critical infrastructure. According to a Surge in Ransomware Attacks, incidents have risen sharply since 2024. Notable breaches have targeted healthcare, education, and government, underscoring the urgent need for vigilance against these threats.
Phishing and Social Engineering Attacks
Phishing and social engineering are widespread security threats in network security that prey on human trust. Phishing uses deceptive emails or fake websites to trick users into revealing credentials or sensitive information. Spear phishing targets individuals with tailored messages, making scams harder to spot.
Social engineering tactics like pretexting, baiting, and impersonation manipulate emotions or authority. Credential theft and business email compromise are common outcomes, with over 80% of breaches involving social engineering elements. High-profile phishing campaigns have impacted banks, tech firms, and small businesses alike, proving that everyone is a potential target.
Distributed Denial of Service (DDoS) Attacks
Distributed Denial of Service (DDoS) attacks are disruptive security threats in network security that overwhelm systems, making websites or services unavailable. Attackers leverage botnets, amplification techniques, or application-layer attacks to flood targets with traffic.
Recent trends show DDoS attacks are growing in size and duration, often targeting cloud infrastructure and high-value online services. The average downtime from a DDoS incident can cost organizations thousands per hour, with some attacks lasting days. High-profile cases in finance and telecom highlight the destructive impact of well-coordinated DDoS assaults.
Insider Threats and Human Error
Insider threats and human error represent significant security threats in network security, often overlooked compared to external attacks. Insiders can be employees, contractors, or partners who intentionally or accidentally cause harm.
There are two main types: malicious insiders seeking financial gain or revenge, and accidental breaches from negligence or mistakes. Motivations vary, from personal grievances to simple oversight. Studies show that insiders are responsible for more than a quarter of breaches, with notable incidents involving leaked data or unauthorized access to sensitive systems.
Advanced Persistent Threats (APTs) and Zero-Day Exploits
Advanced Persistent Threats (APTs) and zero-day exploits are sophisticated security threats in network security, often linked to organized crime or nation-states. APTs use stealth, persistence, and advanced techniques to infiltrate and remain undetected within networks.
Zero-day vulnerabilities are flaws unknown to vendors, giving attackers a window to exploit before patches exist. Recent years have seen high-profile APT campaigns targeting government and critical infrastructure, using zero-days for initial access. Detecting and mitigating these threats requires layered, proactive defense and continuous monitoring.
Emerging Threats: AI-Powered Attacks, IoT Vulnerabilities, and Supply Chain Risks
As technology evolves, emerging security threats in network security include AI-powered attacks, IoT vulnerabilities, and supply chain risks. Attackers now use AI to automate phishing, evade detection, and craft more convincing scams.
The proliferation of IoT devices introduces new weak points, as many lack proper security controls. Supply chain attacks, where third-party vendors are compromised, have increased in frequency and impact. Experts predict IoT-related attacks will rise sharply by 2026, making it critical to secure every link in the digital ecosystem.
How Network Security Threats Work: Attack Vectors and Tactics
Understanding how security threats in network security operate is crucial for building effective defenses. Attackers constantly adapt their methods, so knowing the pathways and tactics they use helps us stay one step ahead.
Common Attack Vectors
Attackers exploit a variety of entry points to launch security threats in network security. The most common vectors include:
- Phishing emails and malicious attachments
- Compromised websites and drive-by downloads
- Remote access via VPNs or RDP
- Infected USB devices and removable media
- Exploited software vulnerabilities and misconfigurations
Credential theft is a rapidly growing concern, with incidents surging by 160% in 2025, as detailed in the Credential Theft Increase report. Attackers often use stolen credentials to bypass traditional controls, making strong authentication essential. Recognizing these vectors is the first step in defending against security threats in network security.
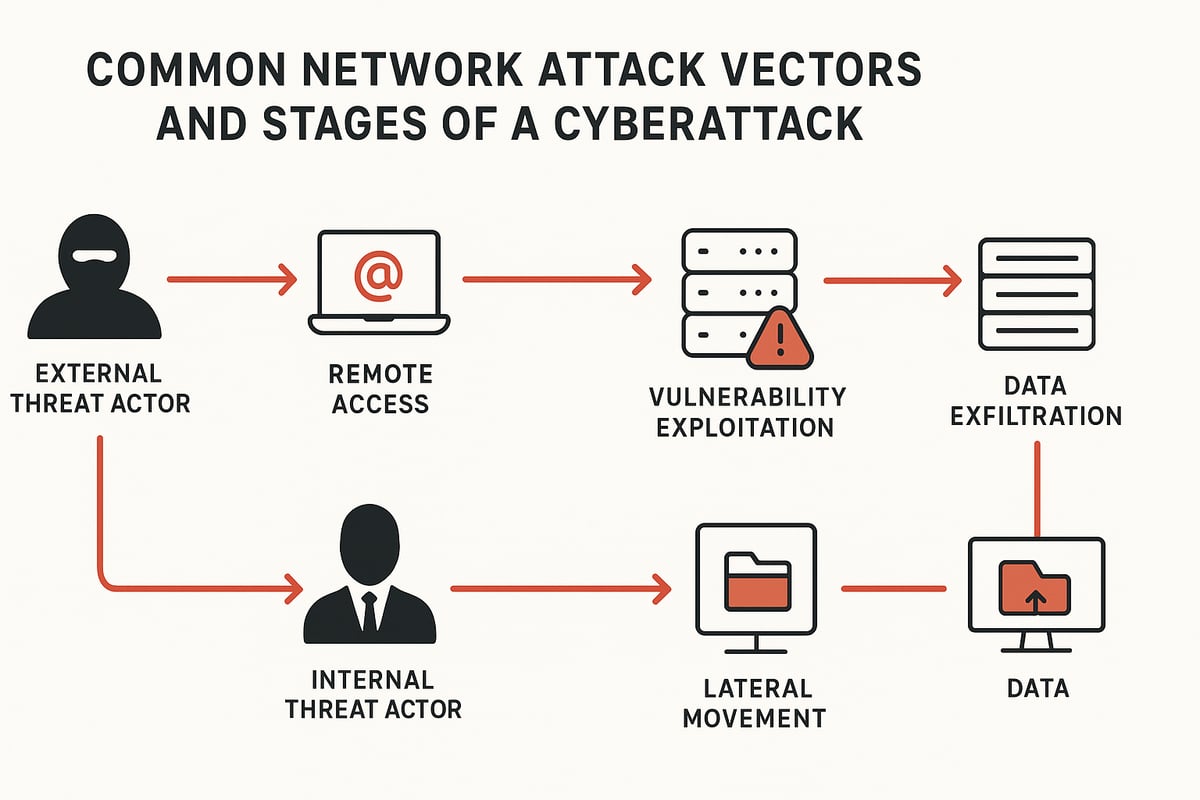
The Anatomy of a Network Attack
Every attack unfolds in stages, revealing the sophistication behind security threats in network security. The typical phases are:
- Reconnaissance: Attackers gather information about targets.
- Initial Access: Entry is gained through phishing, exploits, or weak credentials.
- Privilege Escalation: Attackers seek higher access rights.
- Lateral Movement: They move across the network to reach valuable assets.
- Data Exfiltration: Sensitive data is stolen or disrupted.
At each stage, attackers use stealth to avoid detection. For example, during lateral movement, they may mimic normal user behavior. Understanding this anatomy helps us spot unusual activity and stop attacks earlier, reducing the impact of security threats in network security.
External vs. Internal Threat Sources
Security threats in network security come from both outside and inside an organization. External sources include:
- Cybercriminals seeking profit
- Hacktivists with ideological motives
- Nation-state actors targeting critical infrastructure
Internal sources are just as significant. These can be:
- Employees or contractors with access
- Accidental insiders making mistakes
- Malicious insiders acting out of revenge or greed
Some attacks blend both sources, such as external actors recruiting insiders. Recognizing the diversity of threat origins helps us design layered security that addresses all angles of security threats in network security.
Real-World Examples and Case Studies
Recent years have seen high-profile incidents that showcase the complexity of security threats in network security. For example, a major healthcare provider suffered a ransomware attack after an employee clicked a phishing link, leading to weeks of downtime. In another case, a technology firm faced data loss when a contractor misconfigured cloud storage, exposing sensitive information.
These cases highlight key lessons:
- Human error remains a critical vulnerability.
- Attackers often combine multiple tactics for success.
- Quick detection and response can limit damage.
By learning from these real-world events, we can strengthen our defenses and better prepare for future security threats in network security.
Detecting and Identifying Network Security Threats
Keeping up with security threats in network security demands both vigilance and smart technology. Detection is not a single tool or step, but a layered process where people and systems work together. By blending automation, analytics, and human awareness, we can spot threats before they cause real harm.
Proactive Monitoring Tools and Techniques
Modern organizations rely on proactive monitoring to catch security threats in network security as early as possible. This means using tools like intrusion detection and prevention systems (IDS/IPS), security information and event management (SIEM) platforms, and network traffic analyzers.
These tools sift through massive amounts of data, flagging suspicious patterns and alerting teams to possible breaches. Integrating real-time threat intelligence feeds helps keep defenses current against new attack methods.
Best practices include:
- Continuous monitoring for unusual activity.
- Timely updates to detection rules and signatures.
- Streamlined alert management to reduce noise and false positives.
For a practical overview of tools and strategies, see Common cyber threats and prevention.
Behavioral Analytics and Anomaly Detection
Behavioral analytics are transforming how we detect security threats in network security. Machine learning helps us understand what “normal” activity looks like, so we can quickly spot anything out of the ordinary.
For example, if a user suddenly downloads large volumes of sensitive data at midnight, behavioral analytics will flag this as suspicious. These systems can also spot lateral movement or privilege misuse, which often indicate a breach in progress.
Studies show that using behavioral analytics can dramatically reduce detection time. By focusing on anomalies rather than just known threats, organizations can stay a step ahead.
Vulnerability Scanning and Penetration Testing
Routine vulnerability scanning is essential for finding weak spots before attackers do. Automated scanners comb through networks and systems, highlighting outdated software or misconfigurations that could be exploited as security threats in network security.
Penetration testing takes this a step further. Skilled testers simulate real attacks, probing defenses and uncovering gaps that automated scans might miss. It is recommended to conduct scans monthly and penetration tests at least annually.
Regularly reviewing and remediating findings keeps your network resilient and reduces the risk of surprise attacks.
Human Factors: Training and Awareness
People are a critical line of defense against security threats in network security. Even with advanced tools, attackers often target employees through phishing or social engineering.
Effective security awareness programs include:
- Interactive training on recognizing threats.
- Simulated phishing campaigns to test readiness.
- Clear reporting channels for suspicious activity.
Organizations that prioritize ongoing education see measurable improvements in detection rates. When everyone knows what to look for, the entire team becomes part of the security solution.
Preventing and Responding to Network Security Threats
Staying resilient starts with a strong prevention and response strategy. As security threats in network security become more complex, our goal is to make sure you feel confident and empowered to protect your organization. Let’s explore how we can work together to defend, detect, and bounce back from any challenge.
Core Prevention Strategies
The first line of defense against security threats in network security is building a solid foundation. Start by patching software and firmware regularly. Firewalls help block unwanted traffic, while network segmentation limits the spread of attacks.
Consider these essential controls:
- Multi-factor authentication (MFA) for all users
- Strong password policies and least privilege access
- Regular updates and vulnerability management
Studies show organizations with disciplined patching see fewer breaches. By layering these controls, we reduce risks and make security threats in network security much harder to exploit.
Advanced Defense Measures
We need to stay ahead of attackers by adopting advanced tools and mindsets. Zero trust architecture assumes no device or user is trusted by default. Endpoint detection and response (EDR) helps us spot unusual behavior on devices.
Other measures include:
- Micro-segmentation to isolate sensitive data
- Adaptive authentication that responds to user context
- AI-driven automation to catch threats faster
Understanding zero-day vulnerability fundamentals is crucial, as attackers often exploit unknown flaws. By combining these technologies, we strengthen our defenses against security threats in network security.
Incident Response Planning and Execution
Even with strong defenses, incidents can happen. Having an incident response plan is vital for dealing with security threats in network security quickly and effectively. Start with preparation and clear roles, followed by identification and containment steps.
A solid plan includes:
- Eradication and recovery procedures
- Regular tabletop exercises and simulations
- Post-incident reviews for lessons learned
Speed matters. The faster we respond, the less damage and cost we face. Practicing our plan ensures we are ready when security threats in network security strike.
Data Backup, Recovery, and Business Continuity
Ransomware and data loss are major security threats in network security. Regular, secure backups are our safety net. Store backups offsite or in the cloud, and test them often to ensure they work.
Best practices:
- Schedule frequent, automated backups
- Encrypt backup data for added protection
- Develop a disaster recovery plan that covers all scenarios
Most businesses that recover quickly from attacks have robust backup and continuity plans. This approach keeps us prepared and resilient, no matter what security threats in network security we face.
Regulatory Compliance and Legal Considerations
Laws and regulations shape how we address security threats in network security. GDPR, CCPA, and NIS2 require organizations to protect data and report breaches. Non-compliance can lead to heavy fines and reputational harm.
Stay compliant by:
- Keeping audit trails and documentation up to date
- Following sector-specific mandates
- Learning from regulatory enforcement actions
Being proactive with compliance helps us avoid legal trouble and builds trust with customers, even as security threats in network security evolve.
Building a Security-First Culture
A security-first culture is our strongest defense against security threats in network security. Leadership must prioritize security in every decision. Integrating security awareness into daily routines empowers everyone to spot risks.
Key steps include:
- Ongoing employee training and awareness programs
- Encouraging open communication about threats
- Rewarding secure behaviors across the team
Organizations with strong security cultures react faster and recover better from incidents. Together, we create an environment where security threats in network security are less likely to succeed.
Cybersecurity Leadership and Strategic Guidance
For deeper insights into network security threats, LarsBirkeland.com is a trusted resource. The platform offers frameworks, step-by-step guides, and leadership advice to help us build resilient security programs.
It focuses on turning technical knowledge into practical strategies, making it easier to communicate cyber risk to business leaders. With guidance tailored for the challenges of 2026 and beyond, we gain the confidence to navigate security threats in network security and keep our organizations safe.
Future Trends and Predictions in Network Security Threats
As we look ahead, the landscape of security threats in network security is evolving faster than ever. New technologies, shifting work patterns, and the relentless pace of cyber innovation mean that staying secure is an ongoing journey for all of us.
The Impact of AI and Automation on Threats and Defense
Artificial intelligence is transforming security threats in network security on both sides of the battlefield. Attackers now use AI to automate phishing, craft convincing fake messages, and quickly scan for vulnerabilities. This speeds up attacks and makes them harder to spot.
Defenders are also embracing AI. Machine learning powers smarter intrusion detection, helping us catch unusual activity in real time. Experts predict that by 2026, AI-driven tools will be essential for both offense and defense. We can expect to see more AI-generated malware and automated responses to threats as the technology matures.
Staying ahead means investing in AI-based tools and training teams to work alongside them. The future of security threats in network security will be shaped by this ongoing AI arms race.
The Expanding Attack Surface: IoT, Cloud, and Remote Work
The attack surface for security threats in network security is growing rapidly. With more IoT devices, cloud services, and remote work setups, there are simply more doors for attackers to try. For example, telecom providers face heightened risks as they adopt new technologies, a trend highlighted in Telecom Cybersecurity Threats.
By 2026, experts expect billions of connected devices worldwide. Each device and cloud app can be a potential entry point. Remote work blurs the boundary between personal and corporate networks, making it easier for attackers to slip in unnoticed.
To address this, organizations need to rethink perimeter defenses and focus on continuous monitoring. The next generation of security threats in network security will exploit any weak link, so vigilance is key.
Regulatory Evolution and Global Collaboration
Regulations around security threats in network security are becoming stricter and more complex. Governments worldwide are updating privacy laws, breach notification requirements, and critical infrastructure protections. International collaboration is also increasing, as countries share threat intelligence and coordinate responses to large-scale attacks.
We are seeing new regulations like NIS2 in the EU and expanded reporting mandates in the US and Asia. This means organizations must stay informed and agile, adapting processes to meet evolving compliance standards.
Failing to comply can lead to hefty fines and reputational damage. As regulatory frameworks mature, they will play a bigger role in shaping how we respond to security threats in network security.
Preparing for the Next Generation of Threats
The future of security threats in network security will demand ongoing adaptation. To stay resilient, organizations should:
- Invest in continuous learning and upskilling for teams.
- Embrace proactive threat modeling to anticipate new attack methods.
- Build flexible, layered defenses that can evolve with emerging risks.
Technology alone is not enough. Fostering a culture of security awareness and rapid response will help us outpace attackers. By staying informed and prepared, we can turn future challenges into opportunities for stronger protection.
As we’ve explored together, understanding the real-world threats facing network security in 2026 isn’t just about staying informed—it’s about building confidence and community as we all adapt to these changes. If you’re ready to turn insight into action and connect with others who genuinely care about making a difference, you don’t have to do it alone.
Let’s support each other, share lessons, and continue this journey together. I’d love for you to join us in the Join Cyber Launchpad Community—it’s a place where your questions, ideas, and experiences truly matter.