The digital world in 2026 is more connected than ever, making the need for robust protection urgent for every organization. As threats grow in complexity, the right approach can mean the difference between resilience and risk.
This guide delivers trusted, strategic cybersecurity insights tailored to help you future-proof your business and stay a step ahead. We will explore the evolving threat landscape, proven strategic frameworks, leading assessment models, essential leadership priorities, and the trends shaping tomorrow.
Let’s take action together to build security strategies that stand the test of time.
The Evolving Cyber Threat Landscape in 2026
The digital world is changing at lightning speed, and so are the threats we face every day. In 2026, organizations must keep pace with a threat landscape that’s more complex and aggressive than ever. To build truly resilient defenses, we need to understand what’s coming, adjust our strategic cybersecurity approach, and foster a proactive mindset.
Major Trends and Emerging Threats
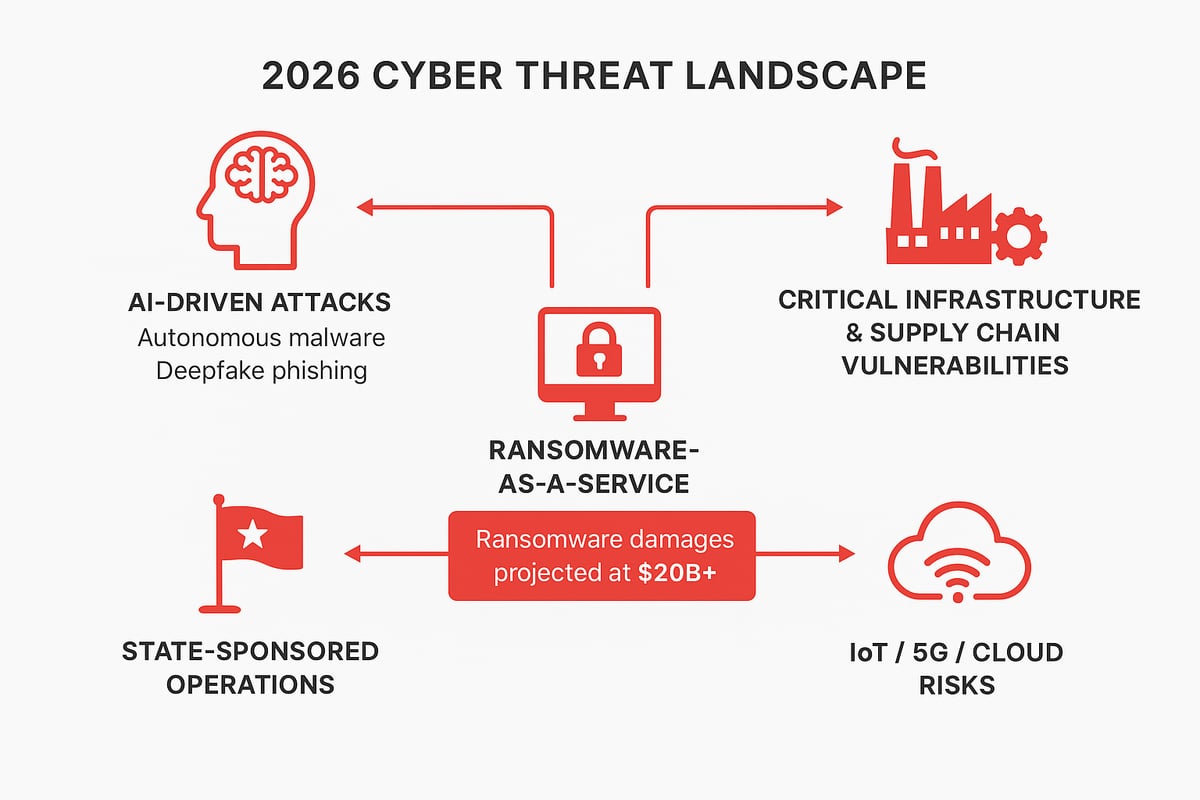
The rise of artificial intelligence in cybercrime is reshaping every aspect of risk. We’re seeing a surge in AI-powered attacks, from self-learning malware to convincing deepfake phishing campaigns that are incredibly difficult to detect. Europol’s 2025 report warned us about the rapid transformation of organized crime through AI, making strategic cybersecurity more urgent than ever.
Critical infrastructure and supply chains are prime targets, with recent global incidents underlining the need for stronger defenses. Ransomware-as-a-service platforms are thriving, enabling even low-skilled attackers to launch sophisticated extortion schemes. State-sponsored operations are on the rise, blurring the line between national security and private sector risk.
As digital transformation accelerates, vulnerabilities in IoT, 5G networks, and cloud environments are expanding the attack surface. According to industry data, global ransomware damages are projected to exceed $20 billion by 2026. Attacks on critical infrastructure have already climbed 30 percent year over year.
For a closer look at these threats and practical ways to defend against them, explore the Cyber Threats and Prevention Strategies guide. It’s a valuable resource for anyone focused on strategic cybersecurity in today’s environment.
Regulatory and Geopolitical Shifts
Regulations are evolving rapidly, reflecting the growing urgency of strategic cybersecurity. Governments worldwide are expanding their cybersecurity mandates, such as the NIS2 Directive in Europe and the U.S. Strategic Cybersecurity Program. These frameworks are raising the bar for organizational responsibility and resilience.
International cooperation is gaining momentum, with countries working together to develop shared norms and response protocols. This cross-border collaboration is essential, as cyber threats rarely respect national boundaries. New privacy laws and stricter compliance requirements mean organizations must align their security strategies with legal obligations.
These shifts are not just about ticking boxes. They’re prompting organizations to rethink how they approach risk, invest in technology, and prioritize the human element in their strategic cybersecurity plans. Adapting to these changes is crucial for staying ahead of attackers and building trust with customers and partners.
Case Examples and Insights
The years 2024 and 2025 brought a wave of high-profile cyber incidents that highlighted new threat vectors. For example, several ransomware attacks on energy grids exposed how interconnected systems can become points of failure. Supply chain breaches, where attackers compromised vendors to reach larger targets, demonstrated the importance of holistic strategic cybersecurity.
Lessons from these events are clear. Nations that responded swiftly, with strong coordination between public and private sectors, minimized damage and restored operations faster. In contrast, organizations without a robust strategic cybersecurity framework struggled to recover and faced lasting reputational harm.
By learning from these cases, we can strengthen our own strategies, anticipate emerging risks, and foster a culture of resilience. Strategic cybersecurity is not just about technology; it’s about people, process, and a commitment to continuous improvement in the face of a shifting threat landscape.
Foundations of Strategic Cybersecurity Planning
In today’s hyper-connected world, a strong foundation is the heart of any strategic cybersecurity journey. Without a clear and resilient plan, organizations risk falling behind and becoming easy targets for evolving threats. Let’s explore what goes into building a future-ready approach that stands the test of time.
The Importance of a National/Organizational Cybersecurity Strategy
Why does strategic cybersecurity matter so much in 2026? The answer is simple: the digital landscape is shifting faster than ever. For both nations and organizations, a well-crafted strategy is the blueprint for resilience, sustainability, and growth.
A national cybersecurity strategic plan (NCSP) brings clarity and direction. It sets a vision for protecting digital assets, aligns security with business goals, and defines risk tolerance. When leaders prioritize strategic cybersecurity, they empower teams to respond rapidly and adapt to unforeseen threats.
Insights from leading research highlight that an NCSP is not just a policy document. It is a living framework, guiding investments, partnerships, and innovation. By connecting technology, people, and processes, organizations foster a culture where strategic cybersecurity becomes part of everyday decision-making.
Key Elements of a Strategic Plan
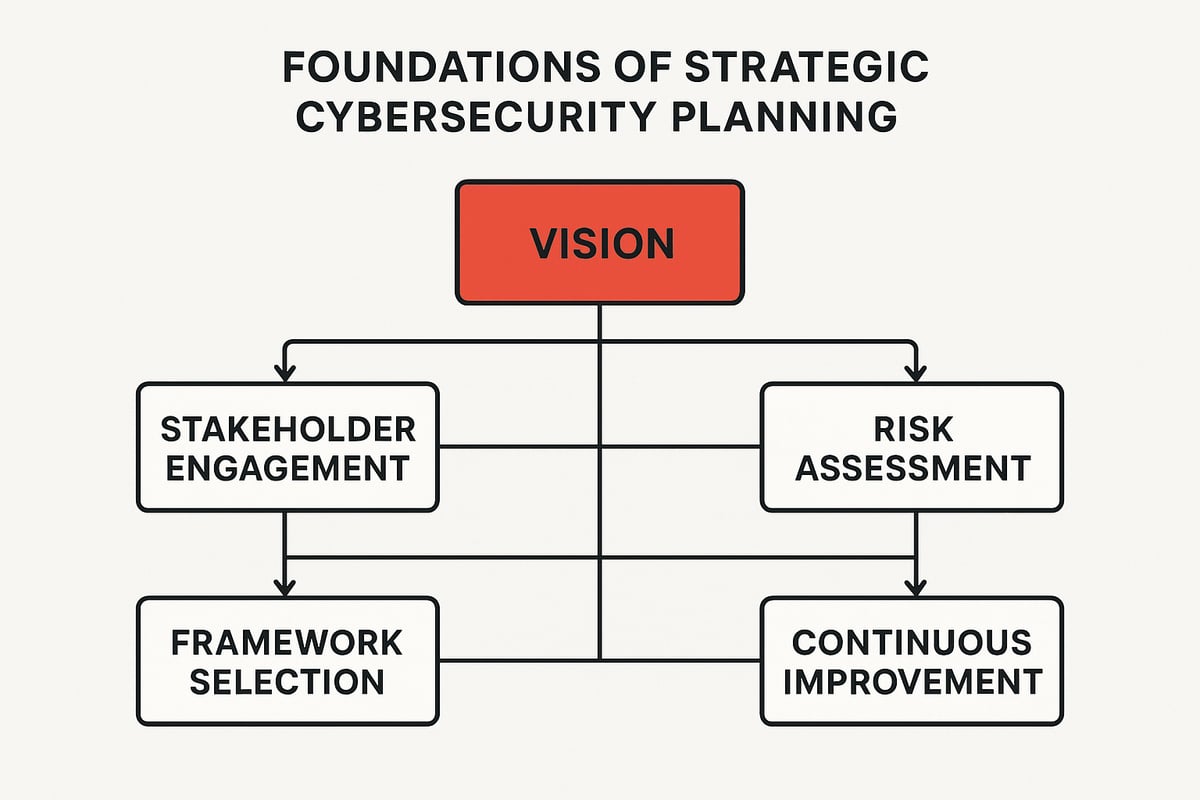
A robust strategic cybersecurity plan starts with a clear vision and mission tailored to your unique context. What are you working toward? Who are the key stakeholders in this journey?
Let’s break down the essentials:
- Vision and Mission: Define what success looks like and how you’ll get there.
- Stakeholder Engagement: Include government, private sector, academia, and civil society to ensure perspectives are broad and inclusive.
- Critical Infrastructure Prioritization: Identify and protect your most valuable information assets.
- Integrated Approach: Address technical, organizational, policy, and legal aspects.
- Continuous Review: Stay agile by regularly updating your plan as threats evolve.
When organizations focus on these core elements, strategic cybersecurity becomes woven into the fabric of their operations. It’s not just about reacting to risks, but proactively shaping a secure digital future together.
Frameworks and Guidelines for Strategy Development
With so many models available, choosing the right frameworks for strategic cybersecurity planning can feel overwhelming. Fortunately, several trusted approaches offer clear paths forward.
Popular frameworks include:
- Commonwealth Approach: Emphasizes collaboration across nations.
- ITU Guidelines: Focuses on national-level cyber defense.
- NIST Cybersecurity Framework: Widely used by enterprises for practical controls and risk management.
- ISO/IEC 27001: Sets international standards for information security management.
Each framework brings different strengths. For example, the NIST Cybersecurity Framework is known for its flexibility and is often adopted by both public and private sector organizations. The ITU Guidelines are favored by countries looking to build national capacity. For a deeper dive into how to select and implement these frameworks, the Strategic Cybersecurity Planning Guide provides step-by-step resources tailored for diverse organizational needs.
Systematic Methodologies for Implementation
Turning strategic cybersecurity plans into reality requires a systematic, stepwise approach. Think of it as building a house: each step strengthens the structure and prepares it for whatever storms may come.
A proven methodology includes:
- Assessment: Evaluate current risks, assets, and readiness.
- Design: Develop policies, controls, and procedures that fit your vision.
- Execution: Put your plan into action, engaging all stakeholders.
- Monitoring: Measure progress and detect new threats early.
- Review: Adapt and refine your strategy regularly.
Public-private partnerships and information sharing are vital. Studies show that over 80 percent of organizations with mature strategic cybersecurity strategies respond to incidents faster and with less disruption. By following a disciplined process, we can ensure our defenses remain strong, agile, and aligned with our evolving goals.
Assessing Cybersecurity Posture: Models, Metrics, and Indices
Understanding where we stand is the first step to building a resilient security program. In 2026, assessing your organization’s cybersecurity posture is not just a checklist item, but a strategic cybersecurity imperative. With threats becoming more complex, having accurate, multi-dimensional insight into your defenses is essential for guiding investments and actions.
Cyber Power, Maturity, and Capability Assessments
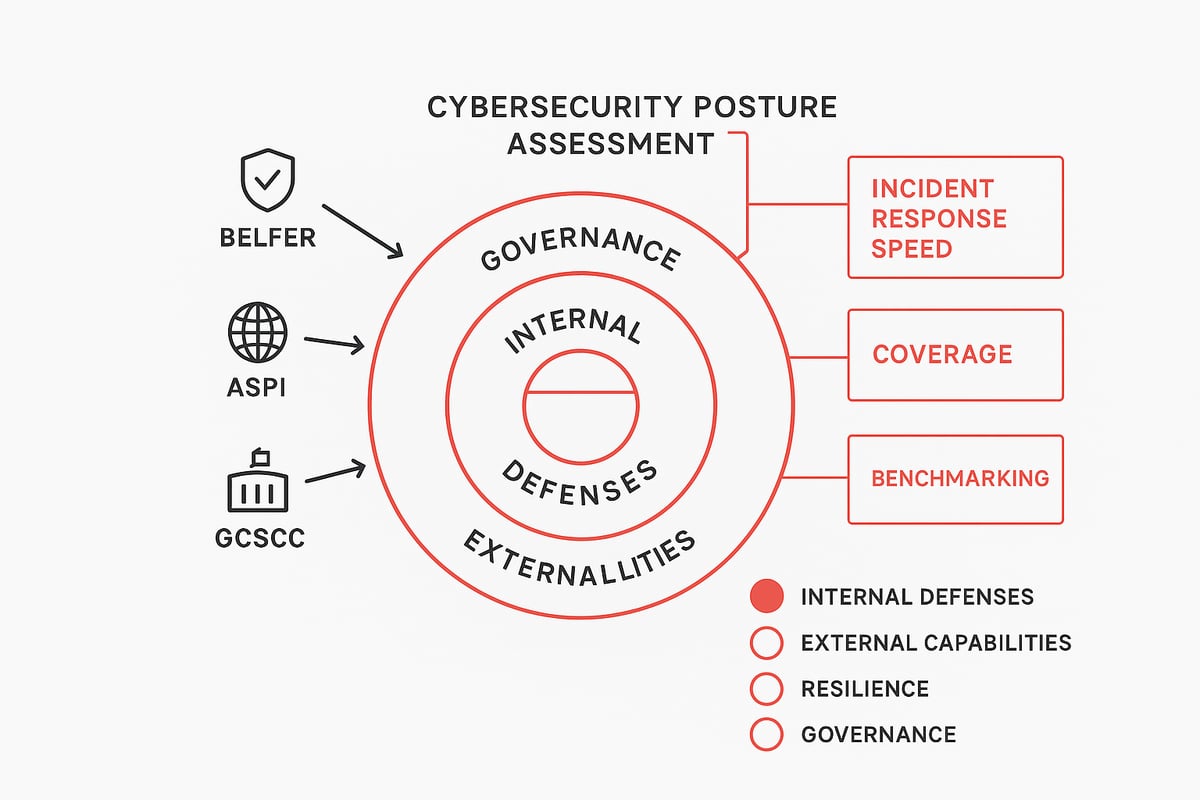
Let’s break down the major models used to measure strategic cybersecurity. The Cyber Power Index evaluates a country’s or organization’s influence and capabilities in cyberspace, capturing both defensive and offensive strengths.
The Cybersecurity Maturity Model, on the other hand, measures how advanced and robust your security processes are, focusing on continuous improvement and risk management. Capability Maturity Models (CMM) dive even deeper, assessing how well processes are defined, managed, and optimized across the organization.
Why does this matter? Strategic cybersecurity requires a multi-dimensional approach. Looking at just one metric, like firewall coverage, will not tell you if your team can respond quickly to a breach or adapt to new threats. By combining these assessments, leaders gain a holistic view of internal defenses, external readiness, and overall resilience.
Metrics often include coverage of critical assets, incident response speed, and adaptability. This approach helps organizations see not just where they are strong, but where strategic cybersecurity investment is needed most.
Leading Assessment Frameworks
Several global frameworks have established standards for evaluating strategic cybersecurity. The Belfer Center National Cyber Power Index ranks nations by their cyber capabilities and intent. The ASPI Cyber Maturity Index compares maturity across defense, governance, and societal engagement.
The Global Cyber Security Capacity Centre (GCSCC) CMM offers a detailed, multi-layered assessment for both nations and enterprises. The EUI Cyber Power Index provides additional benchmarking, focusing on governance and offensive capabilities.
Each framework brings unique strengths. For example, the Belfer Index focuses on national power, while the GCSCC CMM is highly adaptable to organizations of any size. Scoring methods often use weighted criteria, such as:
score = (defense_weight * defense_score) + (governance_weight * governance_score)
Choosing the right framework depends on your strategic cybersecurity goals. Some organizations even combine elements from different models to get a more complete picture.
Practical Application and Examples
How are these models used in real life? Many nations and enterprises benchmark their progress using these indices, identifying gaps and tracking improvement over time. For instance, Qatar adopted a legislative-based maturity model, which significantly improved its national resilience and demonstrated measurable progress in strategic cybersecurity.
Organizations that use maturity models report a 25 percent reduction in breach costs, underscoring the value of structured assessment. If you’re looking for hands-on tools to evaluate your organization’s readiness, the Cybersecurity Posture Assessment Tools offer practical scorecards and checklists tailored for strategic cybersecurity leaders.
Regular benchmarking helps teams stay proactive, not reactive, as threat landscapes evolve.
Limitations and Best Practices
No assessment model is perfect. Data collection can be inconsistent, making comparisons across organizations or countries tricky. Context also matters, as what works for a government agency may not fit a private enterprise. Strategic cybersecurity assessments must be tailored and updated regularly.
Best practices include:
- Periodic reviews to adapt to new threats
- Involving stakeholders from across the organization
- Aligning assessments with broader strategic cybersecurity goals
Keep in mind, the best results come from using these models as living tools, not static reports. Ongoing alignment and review ensure your strategy stays ahead of the curve.
Taxonomy of Strategic Cybersecurity Challenges and Drivers
In today’s digital world, strategic cybersecurity is more than just a technical shield. It’s a collective effort to outpace new risks and keep organizations resilient. As threats evolve and networks become more complex, understanding the full spectrum of challenges and drivers is key to future-proofing our defenses.

Traditional vs. Strategic Cybersecurity Challenges
Let’s start by distinguishing between traditional and strategic cybersecurity challenges. Traditional issues often focus on technical fixes, like patching vulnerabilities, hardening firewalls, or responding to malware. These are vital, but they address only a slice of the larger risk landscape.
Strategic cybersecurity, however, takes a broader view. It considers organizational structure, leadership, and long-term resilience. ScienceDirect highlights a major shift: instead of protecting isolated systems, we now look at entire ecosystems. This includes interconnected supply chains, cloud environments, and even national critical infrastructure.
In this broader context, strategic cybersecurity addresses not only how we defend, but also how we align business goals, legal obligations, and societal needs. This shift helps us anticipate and counter risks that cross organizational and national borders.
New Taxonomy of Strategic Challenges
A modern taxonomy breaks strategic cybersecurity challenges into five domains:
- Technical: These include cloud misconfigurations, IoT vulnerabilities, and software supply chain risks.
- Organizational: Issues like workforce shortages, poor alignment between IT and business, and fragmented leadership.
- Legal: Navigating complex privacy laws, data protection requirements, and regulatory compliance.
- Geopolitical: State-sponsored threats, cross-border data flows, and international cyber norms.
- International: Ecosystem-wide risks involving multiple nations, industries, and global supply chains.
For example, a data breach in one vendor can disrupt hundreds of global companies. Similarly, critical infrastructure like energy grids is now deeply intertwined across borders. Drivers such as rapid technological innovation, evolving regulations, and increasingly sophisticated threat actors constantly reshape this taxonomy.
Implications for Strategy and Policy
Why does this taxonomy matter for strategic cybersecurity? It helps organizations and nations prioritize investments, training, and policy development. Instead of reacting piecemeal, leaders can develop holistic strategies that address multiple domains in tandem.
For instance, aligning technical and organizational measures with legal and geopolitical realities leads to more robust, adaptable defenses. Taxonomies also help clarify where to focus limited resources for maximum impact. According to recent surveys, 60% of security leaders cite organizational alignment as their top strategic cybersecurity challenge.
National strategies, like the CISA Cybersecurity Strategic Plan, increasingly use such taxonomies to guide public-private partnerships and cross-sector collaboration. This integrated approach is vital for staying ahead of rapidly evolving threats.
Case Studies and Insights
Real-world examples show the power of taxonomy-driven strategic cybersecurity. When one nation mapped its risks using a multi-domain approach, it was able to identify overlooked supply chain vulnerabilities and launch targeted training for its workforce.
On the flip side, organizations that failed to bridge the gap between technical fixes and strategic alignment often struggled after major incidents. Lessons learned? Success comes from viewing cybersecurity not as a silo, but as a living, evolving ecosystem.
By applying this taxonomy, both national and enterprise teams can build more resilient, future-ready security programs. Strategic cybersecurity, grounded in a clear understanding of challenges and drivers, empowers us to face tomorrow’s threats with confidence and unity.
Leadership, Workforce, and Culture in Strategic Cybersecurity
In the rapidly changing world of strategic cybersecurity, people remain the most vital asset. As we look ahead to 2026, every organization’s resilience depends on its leaders, workforce, and ability to foster a security-first mindset. Building and nurturing these areas is essential for staying ahead of both known and emerging threats.
Building Skilled and Adaptive Cybersecurity Teams
Creating a robust strategic cybersecurity program starts with people. Organizations must invest in upskilling employees, focusing on areas like AI and machine learning, advanced threat intelligence, and risk management. Communication and collaboration skills are just as crucial, ensuring teams can respond quickly and share insights.
National training programs are expanding, while public-private partnerships and cross-sector exchanges bring fresh perspectives. Encouraging continuous learning helps teams adapt to the evolving threat landscape. As strategic cybersecurity threats become more complex, a skilled and agile workforce becomes a true competitive advantage.
Fostering a Culture of Cyber Resilience
A strong strategic cybersecurity posture depends on more than just technology or policies. Embedding security into daily routines and business processes is vital. Leaders play a key role by championing security at every level, setting clear expectations, and modeling the right behaviors.
Ongoing education, regular awareness campaigns, and hands-on exercises reinforce the importance of security. Drawing from Security Leadership Best Practices, organizations that create an open, supportive culture find it easier to identify and address risks before they escalate. Everyone, from executives to new hires, must feel empowered to take part in the security mission.
Communication and Stakeholder Engagement
Bridging the gap between technical experts and business leaders is essential for effective strategic cybersecurity. Translating complex cyber risks into language that resonates with executives ensures better decision-making and resource allocation.
Successful organizations use cross-functional teams and regular briefings to keep everyone aligned. Communication models that simplify technical jargon help build trust and understanding. When all stakeholders grasp the value of strategic cybersecurity, priorities become clearer and collective action is more effective.
Metrics and Incentives
Measuring progress is crucial for sustaining strategic cybersecurity efforts. Tracking workforce maturity, assessing training effectiveness, and monitoring cultural adoption provide valuable insights for continuous improvement.
Data shows that 70 percent of breaches are linked to human factors. Organizations with a mature security culture experience 40 percent fewer incidents. Offering incentives for proactive behavior and recognizing achievements reinforce positive habits. By focusing on metrics and celebrating progress, organizations can continue strengthening their strategic cybersecurity posture.
If you’d like to connect, collaborate, or join my free community CISO LaunchPad
Future Trends and Strategic Recommendations for 2026
As we look ahead to 2026, the future of strategic cybersecurity is both exciting and challenging. Our digital world is evolving quickly, and so are the threats facing organizations of every size. Staying ahead means anticipating what is coming, adapting our defenses, and building resilience into everything we do.
Anticipating the Next Wave of Cyber Threats
The strategic cybersecurity landscape in 2026 is shaped by new and more complex threats. AI-powered attacks are now mainstream, with criminals leveraging autonomous malware and deepfake technology to bypass traditional defenses. Europol warns that AI-driven crime is transforming the threat environment, making attacks faster and harder to detect. Read more in the Europol warns of AI-driven crime threats report.
Quantum computing is also on the horizon, threatening to break current encryption methods and forcing organizations to rethink their strategies. The growth of cyber-physical threats, especially those targeting smart infrastructure and operational technology, is accelerating. In fact, attacks on IoT and OT environments are projected to rise by 40 percent by 2026.
Strategic cybersecurity now requires us to anticipate not only new tools used by adversaries but also their evolving tactics and procedures. By staying informed and proactive, we can build a strong foundation for the future.
Strategic Investments and Technology Priorities
Investing wisely is central to any strong strategic cybersecurity approach. Organizations are shifting toward adaptive security architectures that can respond quickly to new threats. Zero trust principles are gaining traction, minimizing the risk from internal and external actors alike.
Automation is playing a bigger role, freeing up talented teams to focus on complex problems while machines handle routine responses. Investments in threat intelligence and behavioral analytics are helping us spot attacks faster and understand adversaries’ moves.
Secure-by-design is becoming a guiding principle, ensuring security is built into products and services from the start. Adopting frameworks like the NIST Cybersecurity Framework can help organizations align their technology priorities and processes with global best practices.
These investments are not just about technology—they are about empowering people and processes to work together for resilience.
Policy and Regulatory Evolution
The policy landscape is changing fast, pushing organizations to elevate their strategic cybersecurity programs. New and updated regulations, such as the U.S. Strategic Cybersecurity Program and the EU NIS2 Directive, are setting higher standards for reporting, compliance, and supply chain security.
Privacy laws are expanding, requiring more transparency and stronger protection of personal data. These changes impact how we plan, operate, and audit our security efforts. National and regional strategies are serving as benchmarks, guiding organizations to adopt more robust and future-proof approaches.
Staying ahead requires continuous monitoring of regulatory shifts and a willingness to adapt internal policies quickly. Collaboration with compliance teams and legal experts is now a core part of strategic cybersecurity planning.
Cross-Sector and International Collaboration
No single organization can tackle the challenges of strategic cybersecurity alone. In 2026, collaboration is a must. Public-private partnerships are proving essential, especially when responding to large-scale incidents that cross sector boundaries.
Information sharing networks allow us to learn from each other’s experiences and adapt quickly to new threats. International cooperation is also growing, with nations building alliances to improve resilience and coordinate responses. Countries with strong collaboration frameworks respond 30 percent faster to major incidents.
By embracing a spirit of teamwork, we can share best practices, pool resources, and create a united front against cyber adversaries.
Recommendations for Security Leaders and Organizations
To strengthen your strategic cybersecurity posture in 2026, consider these actionable steps:
- Review and update your security strategy regularly.
- Invest in workforce development and continuous learning.
- Embrace frameworks like the NIST Cybersecurity Framework to guide improvements.
- Prioritize proactive risk management and scenario planning.
- Foster a culture of security across all levels of the organization.
Ask yourself: Are we prepared for tomorrow’s threats? Do we have the agility to adapt? Are our people empowered to respond? By focusing on these questions, leaders can drive meaningful progress.
Preparing for the Unknown
The only certainty in strategic cybersecurity is uncertainty itself. Black swan events—unexpected and disruptive attacks—require us to be ready for anything. Building robust crisis management and incident response plans is critical.
Organizations should develop and regularly test playbooks for various scenarios, ensuring everyone knows their role in a crisis. Encouraging adaptability and innovation will help teams pivot when the unexpected happens.
By nurturing a growth mindset and staying open to new ideas, we can prepare for whatever the future brings. Strategic cybersecurity is not a destination, but an ongoing journey we must take together.
As we look ahead to 2026 and all the new challenges and opportunities in cybersecurity, it’s clear that none of us can tackle this complex landscape alone. Whether you’re building strategic plans, translating technical risks for leadership, or simply seeking clarity in the noise, being part of a supportive, like minded community makes all the difference. If you’re ready to connect with peers who truly get it, share real world stories, and access practical frameworks that actually move the needle, let’s take this journey together.
Come join us at Join CISO Launchpad Community — we’re stronger when we lead and learn as one.